Chapter 17: Counter-Jamming Operations and Link Budget
Spectrum Superiority Operations: The Liberation Signal Architecture
KEY FINDINGS — Chapter 17: Counter-Jamming Operations and Link Budget
Evidence-tier key: see front matter for [L1]–[L4] definitions.
- The doctrine-core surface of this chapter is the link-budget method: identify gains, losses, threshold margin, and the highest-leverage interventions before talking about alliance or testimony layers [L1 methodology, L2 application]
- The control problem is layered rather than singular: corrupted reference, attenuation, injected narratives, parasitic drain, and receiver suppression compound to keep populations locked [L2]
- The escape-probability and population-threshold numbers in this chapter are derived or illustrative outputs from the model. They are not measured civilizational statistics and should not be presented that way [L2-L3]
- Pull-off and pull-back dynamics give a disciplined account of breakthrough, regression, and cumulative integration without requiring a dramatic narrative voice [L1 methodology, L2 application]
- The alliance and starseed sections later in the chapter remain scenario intelligence. They may widen planning space; they are not required to use the doctrine core [L3]
_________________________________
Chapter 16 described the denial architecture. This chapter supplies the first proactive response.
A leadership reader can use three things here immediately: the link-budget method, the counter-jamming taxonomy, and the rule that receiver quality matters more than rhetorical volume. The later alliance and testimony material remains in the chapter, but it is fenced as scenario intelligence rather than treated as a prerequisite for doctrine use.
17.1 The Locking Problem: Why Self-Extraction is Nearly Impossible
17.1.1 Review of the Adler Equation
The starting point is still the Adler equation from Chapter 12: \[ \frac {d\phi }{dt} = \Delta \omega - \omega _L \sin (\phi ) \]
|
Variable | Description |
|
\(\phi \) | phase difference between local oscillator and injected signal |
|
\(\Delta \omega = \omega _{inj} - \omega _0\) | frequency detuning |
|
\(\omega _L\) | locking bandwidth |
For a driven oscillator, \[ \omega _L = \frac {\omega _0}{2Q} \cdot \frac {V_{inj}}{V_0} = \frac {\omega _0 R}{2Z_0} \cdot \frac {V_{inj}}{V_0} \]
Stable lock exists when \(|\Delta \omega | \leq \omega _L\). Two operational consequences follow directly.
- 1.
- Higher \(Z_0\) and higher \(Q\) narrow the capture range.
- 2.
- Stronger injected power and lower personal power widen it.
That is the whole doctrine foundation for the rest of the chapter.
17.1.2 The Layered Control Architecture
The problem is not one injected narrative. It is a stacked control environment in which several mechanisms reinforce one another.
|
Layer | Function | RF analogue | Doctrine use |
|
corrupted reference | provides the wrong orienting signal | bad LO / false reference | explains why self-correction can be internally distorted |
|
paradigm cage | attenuates competing interpretations | shielding / attenuation | explains why alternative signals arrive weak or late |
|
narrative injection | maintains synchronized belief states | injection lock | explains stable population capture |
|
parasitic drain | reduces available receiver power | coupled loss / extraction | explains weakened recovery capacity |
|
receiver suppression | keeps capture range broad | lowered \(Z_0\), low Q | explains persistent vulnerability |
The layers matter because they multiply, not merely add. A population already low in receiver quality is easier to lock. A locked population is easier to shield. A shielded population has less access to counter-signals capable of improving receiver quality.
17.1.3 Why Escape Probability Compounds
The doctrine claim here should be stated carefully. The system is structurally difficult to escape because several low-probability requirements must line up at once.
A minimal escape path requires all of the following: 1. access to a practice or reference that narrows lock range; 2. enough persistence to keep using it while still under lock; 3. enough retained power to withstand drain and regression; 4. enough exposure to a counter-signal to make the new lock stable.
That is why a product-style probability cascade is useful: \[ P_{escape} = P_{find\_practice} \cdot P_{maintain\_practice} \cdot P_{resist\_drain} \cdot P_{access\_counter} \]
The familiar 0.0015% figure in this chapter should therefore be read narrowly. It is an illustrative compounding example, not a measured human base rate. Its job is to show why partial progress often fails, not to claim a calibrated planetary statistic.
17.1.4 The Closed-Loop Trap
The central trap is diagnostic. A locked receiver often evaluates reality through the same corrupted reference that is creating the lock.
That is why a purely internal solution is unreliable. If the mixer reference is wrong, clean input can still produce distorted output. In doctrine terms, self-diagnosis under heavy capture cannot be assumed trustworthy without an external reference, plural verification, or a protocol that measurably improves receiver quality.
17.1.5 Pull-Off, Regression, and Ratchet Gain
Electronic warfare already has a clean analogy for breakthrough-then-regression: pull-off and pull-back. The target is temporarily drawn away from the original track, then reacquired if the shift cannot be sustained.
That maps cleanly onto temporary spiritual or psychological breakthroughs. A retreat, psychedelic event, crisis, or contemplative opening may move the receiver outside the old lock range for a time. If nothing stabilizes the new state, the system is pulled back by habit, social reinforcement, fear, and institutional gravity.
The useful doctrine point is not the drama of the event. It is the ratchet condition.
\[ Q_{n+1} = Q_n + \Delta Q \cdot \mathbb {1}[ ext{integration occurs during pull-off}_n] \]
A breakthrough matters only if it produces durable receiver improvement before regression completes. That is why Chapter 19 matters operationally: integration infrastructure determines whether a pull-off event becomes accumulated gain or just another transient excursion.
17.2 Electronic Counter-Countermeasures (ECCM): The Liberation Toolkit
17.2.1 ECCM Techniques Mapped to Consciousness Liberation
ECCM (Electronic Counter-Countermeasures) in military RF systems are techniques for defeating jamming and maintaining communication under adversarial conditions. They map directly to consciousness liberation:
|
ECCM Technique | RF Implementation | Consciousness Liberation Analog |
|
Burn-through | Increase transmit power until it exceeds jammer | Raise Source signal strength; high-coherence transmission |
|
Frequency hopping | Rapidly change operating frequency | Multi-paradigm awareness; don’t stay locked to one narrative |
|
Spread spectrum | Distribute signal across wide bandwidth | Distributed awakening across population; no single target |
|
Null steering | Point antenna null toward jammer | Attention discipline; tune out control signals |
|
Alternative reference | Switch to different LO source | Connect to uncorrupted guidance (clean LO) |
|
Diversity reception | Multiple receivers for same signal | Cross-validate sources; triangulate truth |
|
Stochastic resonance | Inject noise at nonlinear threshold to aid weak-signal detection | Chaos in awakening; breakdown-to-breakthrough transitions |
17.2.1a Processing Gain and Anti-Jam Margin In spread spectrum communications, the cooperative receiver can collapse the spread signal back to information bandwidth, gaining a processing gain advantage over any jammer that must cover the full spread bandwidth (Adamy, EW 102, 2004, Ch 6.9, pp. 141–142):
\[ G_p = 10\log _{10}\!\left (\frac {BW_{spread}}{BW_{info}}\right ) \quad \text {(dB)} \]
The anti-jam margin (AJM) — the excess protection available after accounting for system losses and required output SNR — is:
\[ AJM = G_p - L_{sys} - SNR_{out,req} \quad \text {(dB)} \]
where \(L_{sys}\) captures implementation losses and \(SNR_{out,req}\) is the minimum output quality needed for reliable reception.
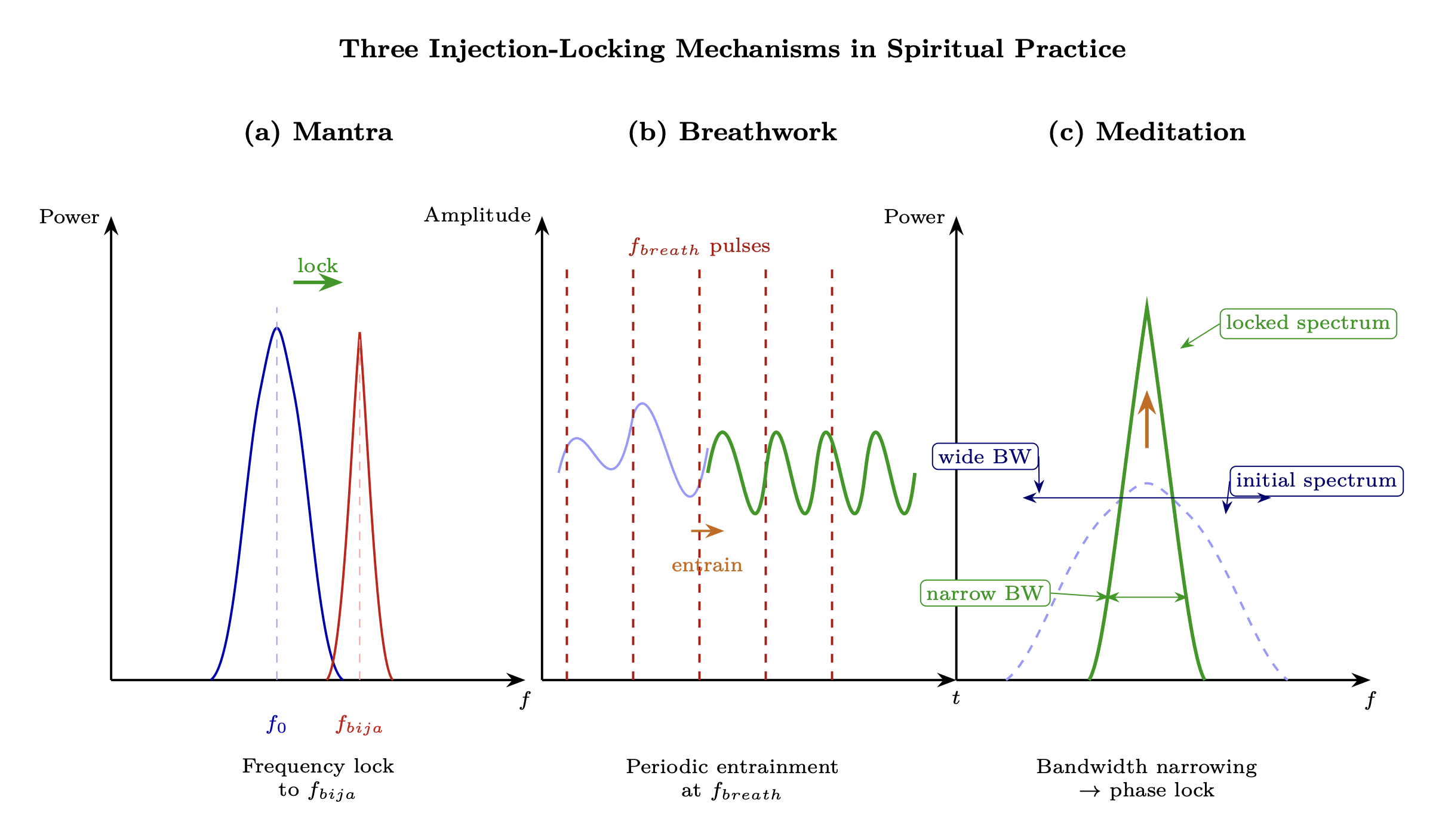
Consciousness mapping: A practitioner who integrates multiple traditions — meditation, breathwork, contemplative prayer, somatic work, plant medicine — spreads their consciousness practice across a wider bandwidth than a single-tradition practitioner. The cooperative receiver (the practitioner’s own integrated framework) can collapse this spread practice back to coherent insight, while the control architecture must jam across the full practice bandwidth or accept that some channels will be clear.
|
Practice Approach | \(BW_{spread}\) | \(BW_{info}\) | \(G_p\) | Anti-Jam Implication |
|
Single tradition only | Narrow | Narrow | ~0 dB | Spot-jammable: suppress one tradition, suppress all access |
|
2–3 complementary traditions | Moderate | Same | ~5–8 dB | Requires multi-topic suppression; some redundancy |
|
Eclectic integral practice (5+) | Wide | Same | ~12–18 dB | Broadband jamming required; concentrated suppression fails |
FHSS vulnerability note: Predictable hop patterns — formulaic practice rotation (Monday meditation, Wednesday yoga, Friday breathwork, never varying) — can be followed by adaptive jammers (Adamy, EW 102, 2004, Ch 6.9.1, pp. 142–143: follower jamming). If the control architecture can predict the practitioner’s next “hop frequency,” it can pre-position suppression. Genuine randomization — following intuition, varying practice in response to inner guidance rather than external schedule — defeats follower jamming by making the hop pattern unpredictable.
Prediction (P-GP): Multi-tradition practitioners should show greater resilience to single-vector narrative suppression campaigns than single-tradition practitioners, and practitioners with genuinely intuition-guided practice variation should show greater resilience than those with fixed schedules. [L2-L3]
That these ECCM techniques have real-world consciousness analogs is not purely theoretical. Begich & Manning (2002) [L3] document HAARP ionospheric research and its claimed capacity to alter human mental states via ELF wave injection—demonstrating that at least one state actor has explored literal injection locking of neural oscillators through an environmental carrier (see Chapter 12, Section 12.6.2 for the full treatment). If injection locking can be weaponized, the corresponding ECCM countermeasures (frequency hopping, spread spectrum, null steering) become operational necessities.
EMSO doctrine. Counter-jamming is the electronic protection (EP) response to electronic attack (EA) — the three-branch taxonomy per Adamy (EW 102, 2004, Ch 1; see Chapter 12, Section 12.1.4). The techniques in this chapter — frequency hopping (practice diversity), spread spectrum (multi-tradition integration), adaptive nulling (selective attention) — are direct EP implementations applied to the consciousness spectrum. The processing gain equation (Section 17.2.1a) quantifies the spread-spectrum advantage, and the link budget analysis quantifies whether the protection margin is sufficient for signal recovery.
17.2.2 Why External ECCM is Required
Each control layer requires specific counter-measures that the locked individual cannot provide:
Layer 1: Corrupted LO \(\relax \to \) Requires Alternative LO
- Individual cannot generate clean reference from within corrupted system
- External clean LO must be provided
- This is the function of higher-density benevolent beings
Layer 2: Paradigm Cage \(\relax \to \) Requires Cage Breach
- Individual inside cage cannot perceive what’s being blocked
- External signals must penetrate or circumvent shielding
- Disclosure events, direct experience, paradigm cracks
Layer 3: Injection Lock \(\relax \to \) Requires Counter-Injection
- Locked oscillator pulled back by any escape attempt
- External signal must exceed control signal (burn-through)
- Or provide pathway to frequency hop away from lock range
Layer 4: Parasitic Coupling \(\relax \to \) Requires Energy Supply
- Drained oscillator too weak to maintain independent oscillation
- External energy infusion required
- “Spiritual support” = power supply to starving oscillator
This is why the “positive alliance” exists: to provide the external counter-measures that locked individuals cannot generate internally.
17.2.3 The ECCM Stack for Human Liberation
A complete liberation counter-jamming system requires:
LAYER 7: SOURCE SUPPORT (Burn-through power) \(\downarrow \) LAYER 6: GALACTIC COORDINATION (Alternative LO network) \(\downarrow \) LAYER 5: STELLAR TRANSMISSION (Solar/stellar ECCM) \(\downarrow \) LAYER 4: PLANETARY INFRASTRUCTURE (Grid activation) \(\downarrow \) LAYER 3: SURFACE OPERATIONS (Ground crew) \(\downarrow \) LAYER 2: NETWORK COHERENCE (Community arrays) \(\downarrow \) LAYER 1: INDIVIDUAL UPGRADES (Receiver improvements)
Each layer provides specific ECCM capability. The following sections detail each component.
_________________________________
Speculative extension (L4–L5). The following section applies the framework to insider testimony that cannot be independently verified. The link-budget mathematics in §17.9 stands regardless of whether these claims are accurate. Readers may skip to §17.7 without loss of analytical continuity.
17.3 The Positive Alliance: Counter-Transmission Infrastructure
Doctrine-Core Mechanics. The doctrine-safe content in this section is the structural requirement for an external clean reference: if a population is locked to a corrupted LO, liberation requires an alternative reference chain, distributed relay capacity, and enough coherent gain to compete with the jammer.
Scenario-Intelligence Layer. The named factions and organizational claims below are admissible for exploratory planning and scenario framing. They are not adjudicated operational fact.
Handling and Use Restrictions. Downstream use must not outrun the evidence tier. Retain the structural roles for planning; do not operationalize named entities, timelines, or alliance hierarchies as confirmed unless they receive independent corroboration.
17.3.1 Hierarchy of Benevolent Transmitters
The control system operates through a hierarchy (Source \(\relax \to \) Corrupted intermediaries \(\relax \to \) Control infrastructure \(\relax \to \) Individual lock). The liberation system operates through a parallel benevolent hierarchy:
|
Tier | Entity Type | RF Function | Transmission Range |
|
0 | Source/Infinite Creator | Master oscillator | Infinite (always available) |
|
1 | 7th Density collectives | Primary transformer | Galactic |
|
2 | 6th Density benevolent groups | Secondary distribution | Stellar clusters |
|
3 | 5th Density coordinators | Tertiary matching | Solar system |
|
4 | 4th Density positive ET | Local amplifiers | Planetary |
|
5 | Incarnated high-\(Z_0\) souls | Ground repeaters | Local/regional |
The Source signal was never blocked; it continues to broadcast. What was corrupted was the transduction chain (Ch 15). The positive alliance provides an alternative transduction chain that bypasses the corrupted LO.
17.3.2 Galactic Federation as Alternative LO
In the superheterodyne model (Ch 3), the Adamic LO was corrupted, causing all downstream mixing to produce corrupted output. The Galactic Federation (or equivalent benevolent coordination body) is an alternative local oscillator network: \[ f_{IF,clean} = f_{RF,Source} - f_{LO,Federation} \] vs. \[ f_{IF,corrupted} = f_{RF,Source} - f_{LO,corrupted} \] The clean LO produces correct IF; the corrupted LO produces phase-shifted, noise-contaminated IF.
For individuals to switch LOs, they must:
- 1.
- Recognize the existing LO is corrupted (awareness)
- 2.
- Tune to the alternative LO frequency (resonance)
- 3.
- Establish phase lock to clean reference (practice)
- 4.
- Maintain lock against interference (sovereignty/\(Z_0\))
Epistemic Note: The “Galactic Federation” terminology comes from channeled material (Ra, Bashar, Swaruu, etc.) and insider testimony (Goode, Smith). Whether this represents actual organizational structure, metaphorical framework, or projection cannot be determined from available evidence. The RF model works regardless—some alternative clean LO source exists for those who successfully escape lock.
17.3.3 SSP Faction Spectrum
The Secret Space Program testimonies describe multiple factions with varying orientations:
|
Faction Type | Orientation | RF Role | Evidence Source |
|
Dark Fleet | Service-to-self | Maintains control infrastructure | Goode, Tompkins |
|
Solar Warden | Mixed/transitioning | Partial disclosure, limited liberation | Goode |
|
Sphere Being Alliance | Service-to-others | ECCM coordination, timeline management | Goode |
|
Anshar | Service-to-others | Ground-based support, genetic preservation | Goode |
|
Earth Alliance | Mixed | Surface coordination | Multiple |
Not all “positive” factions are fully aligned. Some pursue limited disclosure (controlled partial ECCM) rather than full liberation.
Epistemic Note: SSP testimony is difficult to verify. The value of this framework is organizational—it maps alleged structures to RF functions. Validation requires future disclosure events that either confirm or contradict the structural claims.
17.3.4 Inter-Alliance Coordination as Phased Array
Multiple positive factions, when coordinated, form a phased array transmitter (Ch 11): \[ G_{alliance} = N_{factions} \cdot r_{alliance}^2 \] Note: This chapter uses \(r\) for the coherence order parameter, consistent with the Kuramoto formulation in Chapter 11.
Where:
| Variable | Description |
| \(N_{factions}\) | Number of coordinated benevolent groups |
| \(r_{alliance}\) | Coherence (phase alignment) between factions |
Array gain increases with:
- More factions joining the alliance (N\(\uparrow \))
- Better coordination between factions (\(r\)\(\uparrow \))
Alliance coherence is imperfect. Different factions have different timelines, methods, and priorities, reducing effective array gain.
The Sphere Being Alliance (per Goode testimony) allegedly acts as the array controller, coordinating phase alignment between disparate positive factions to maximize coherent transmission power.
_________________________________
17.4 Starseeds & Lightworkers: Embedded High-Q Oscillators
Doctrine-Core Mechanics. The doctrine-core claim here is modest: some individuals may function as unusually resilient, high-coherence repeater nodes whose main value is local signal preservation, reference stabilization, and community-scale gain.
Scenario-Intelligence Layer. The starseed framing provides a planning language for thinking about such nodes, activation triggers, and distributed network topology. It remains a scenario layer rather than an adjudicated population taxonomy.
Handling and Use Restrictions. Use these models for exploratory segmentation, not identity assignment. No institution should treat subjective self-identification or testimony as sufficient proof of role, origin, or mission status.
17.4.1 The Starseed Function
Starseeds are souls originating from higher-density or different planetary systems who incarnate on Earth with specific mission parameters. In RF terms, they are pre-positioned repeater nodes: \[ \text {Starseed} = \text {High-}Z_0\text { oscillator} + \text {Mission encoding} + \text {Activation trigger} \] Primary functions:
- 1.
- Local oscillator injection: Provide clean reference frequency in immediate environment
- 2.
- Counter-signal amplification: Boost weak truth signals through personal coherence
- 3.
- Network nodes: Connect to other starseeds forming distributed array
- 4.
- \(Z_0\) demonstration: Model high-impedance operation for surrounding population
17.4.2 Starseed vs. Standard Human Specifications
|
Parameter | Standard Human | Starseed | Significance |
|
Q factor (baseline) | 3-5 | 8-15 | Narrower lock bandwidth, harder to capture |
|
\(Z_0\) (baseline) | Low-Medium | Medium-High | Greater sovereignty, better Source match |
|
\(f_0\) range | Narrow | Narrow | Tighter resonance; harder to detune |
|
Activation potential | Standard | Enhanced | DNA encoding for staged activation |
|
P_osc (oscillator power) | 0.3-0.5 | 0.5-0.9 | Stronger signal for local injection |
|
Paradigm susceptibility | High | Lower | Pre-existing alternative frameworks |
|
LO flexibility | Low | High | Can switch reference sources |
The higher baseline \(Z_0\) means starseeds are harder to fully capture by standard control mechanisms. They may be partially locked but retain oscillation capacity that can be activated.
17.4.3 Activation Sequence
Starseed activation follows a staged sequence:
|
Stage | Trigger | RF Process | Observable Signs |
|
1. Dormant | Incarnation complete | Oscillator present but damped | Normal-appearing life |
|
2. Stirring | External resonance contact | Q begins rising | Synchronicities, seeking |
|
3. Awakening | Threshold \(Z_0\) reached | Lock begins breaking | Paradigm crisis, downloads |
|
4. Active | Mission parameters engage | Full oscillation, transmission begins | Teaching, healing, creating |
Activation energy required: \[ E_{activation} = E_{threshold} - E_{current} = \frac {1}{2}L(I_{threshold}^2 - I_{current}^2) \] The gap between current state and activation threshold must be bridged. This can occur through:
- External high-coherence contact (another activated starseed)
- Accumulated practice reaching threshold
- Crisis that shatters lock, allowing reconfiguration
- Coordinated “activation waves” from alliance
17.4.4 Distribution Strategy: Small-World Network
Starseeds are not randomly distributed; they are positioned according to small-world network topology:
- High clustering Starseeds tend to cluster in regions/communities
- Short path length Any point on Earth is within few “hops” of a starseed
- Hub nodes Some starseeds serve as high-connectivity hubs
Network effectiveness equation: \[ \eta _{network} = \frac {C_{clustering}}{L_{path}} \cdot N_{activated} \] Where:
| Variable | Description |
| \(C_{clustering}\) | Clustering coefficient |
| \(L_{path}\) | Average path length |
| \(N_{activated}\) | Number of activated starseeds |
Estimated starseed population: 50-100 million globally (varying estimates) Estimated activated: 1-5 million (highly uncertain)
No rigorous census exists; these figures reflect estimates circulating in alternative research communities and should be treated as order-of-magnitude placeholders.
The gap between incarnated and activated is the “sleeper” population awaiting triggers.
Epistemic Note: “Starseed” is a term from New Age literature with no scientific definition. The RF model treats it as a functional category—individuals with measurably different baseline parameters and activation potential. Whether this represents actual ET soul origin, natural human variation, or self-fulfilling identification cannot be determined empirically.
17.4.5 Lightworkers as Activated Amplifiers
Lightworkers—individuals consciously working toward collective awakening—are either activated starseeds or standard humans who have raised their \(Q\) above typical baseline through sustained practice. Higher \(Z_0\) enables tuning to higher-frequency Source signals (the density carrier \(f_d\) scales with impedance; see Chapter 2, Section 1.3). In RF terms, they are local signal amplifiers: \[ P_{local} = P_{received} \cdot G_{lightworker} \] Where:
- \(P_{received}\) = incoming signal from higher sources
- \(G_{lightworker}\) = personal amplification gain
Gain factors:
|
Factor | Contribution | Method to Increase |
|
Personal \(Z_0\) | Sets maximum gain | Wisdom (L\(\uparrow \)), shadow work (C\(\downarrow \)) |
|
Practice consistency | Gain stability | Regular meditation, coherence work |
|
Network connection | Coupling efficiency | Community involvement |
|
Service orientation | Impedance match to Source | Reduce self-interest noise |
Individual gain equation: \[ G_{lightworker} = 10 \log _{10}\left (\frac {Z_0}{Z_{0,baseline}} \cdot r_{practice} \cdot \eta _{service}\right ) \text { dB} \] The distinction between starseed and lightworker is functional, not categorical. A lightworker is any oscillator operating above baseline \(Q\) and actively transmitting. Many lightworkers are activated starseeds; others are standard humans who reached high-\(Q\) operation through dedicated practice.
_________________________________
17.5 Ground Operations: Collective ECCM Implementation
17.5.1 Mass Meditation as Coherent Pulse
When multiple individuals meditate simultaneously with shared intention, they form a coherent transmitter array (Ch 11): \[ P_{event} = P_{individual} \cdot N_{participants} \cdot r_{event}^2 \] Where:
- \(P_{individual}\) = average individual power
- \(N_{participants}\) = number of participants
- \(r_{event}\) = coherence during event (0-1)
Collective gain: \[ G_{collective} = 10 \log _{10}(N \cdot r^2) \text { dB} \] Example calculation:
- N = 1,000,000 participants
- \(r\) = 0.3 (moderate coherence, typical for loosely coordinated event)
- \(G_{collective} = 10\log _{10}(N \cdot r^2)\). For N = 1,000,000 and \(r\) \(\approx \) 0.2–0.4 (moderate coherence range): \(G_{collective}\) \(\approx \) 45–55 dB (central estimate ~50 dB at \(r\) = 0.3)
This amounts to roughly 100,000x power amplification over a single individual.
Evidence for mass meditation effects:
- Global Consciousness Project: Statistically significant RNG deviations during coordinated global events
- HeartMath studies: Measurable coherence effects in group meditation settings
- TM research: Claimed crime reduction during large meditation assemblies (controversial, needs replication)
17.5.2 Grid Work and Ley Line Activation
From Chapter 14, megalithic infrastructure was designed as a planetary resonant network but went dormant after the Fall. Grid work attempts to reactivate it:
Mechanism:
- 1.
- Identify dormant nodes (sacred sites, power spots)
- 2.
- Inject coherence through group meditation at site
- 3.
- Establish standing wave patterns
- 4.
- Connect nodes through ley line transmission
Reactivation equation: \[ P_{node} = Q_{site} \cdot P_{injected} \cdot \left (1 - e^{-t/\tau _{activation}}\right ) \] Where:
- \(Q_{site}\) = quality factor of resonant site (higher for intact sites)
- \(P_{injected}\) = power from meditation group
- \(\tau _{activation}\) = time constant for site activation
Current status: Partial reactivation reported at some sites. Full network activation would require:
- Sufficient number of high-\(Z_0\) practitioners
- Coordinated timing across multiple sites
- Knowledge of original operating frequencies (largely lost)
_________________________________
Speculative extension (L4–L5). The following section applies the framework to insider testimony that cannot be independently verified. The link-budget mathematics in §17.9 stands regardless of whether these claims are accurate. Readers may skip to §17.7 without loss of analytical continuity.
17.6 SSP Hardware: Technological Counter-Jamming
17.6.1 Sphere Being Barrier as Band-Pass Filter
Per Goode testimony, the Sphere Being barrier (giant spheres positioned around the solar system circa 2012) acts as a frequency-selective barrier:
Band-pass filter model: \[ H(f) = \frac {1}{1 + jQ\left (\frac {f}{f_0} - \frac {f_0}{f}\right )} \] Filter characteristics:
- Pass band Frequencies supporting consciousness evolution
- Stop band Frequencies enabling parasitic extraction and control injection
- Transition band Mixed transmission depending on intent
| Signal Type | Barrier Response | Effect |
| Source/positive transmission | Pass | Full power through |
| Neutral information | Pass | Normal propagation |
| Control/parasitic signals | Attenuate | Reduced power reaching Earth |
| Escape attempts (negative entities) | Block | Quarantine enforcement |
Quarantine function: The barrier also prevents certain negative entities from leaving the solar system, enforcing containment while liberation proceeds.
Epistemic Note: The sphere barrier is reported only by Goode and a few corroborating sources. No independent verification exists. The RF model is consistent with reported functions but does not confirm actual existence.
17.6.2 Solar Flash as Burn-Through Event
Multiple sources predict a solar event (coronal mass ejection, micronova, or consciousness pulse) that would act as system-wide ECCM:
Burn-through model: \[ P_{flash} >> P_{control} \implies \text {All locks broken simultaneously} \] When transmitted power far exceeds jamming power, the jammer is overwhelmed and lock is lost.
Solar flash characteristics (predicted):
|
Parameter | Estimated Value | Effect |
|
Power increase | 10-100\(\times \) normal | Exceeds all control injection |
|
Duration | Hours to days | Sufficient for new locks to form |
|
Spectrum | Broadband + consciousness frequencies | Affects all densities |
|
Selectivity | Based on \(Z_0\) threshold | Different effects by development level |
\(Z_0\)-dependent effects: \[ \text {Experience} = f(Z_0, P_{flash}) \]
- Low \(Z_0\): Potentially damaging (system overload)
- Medium \(Z_0\): Intense but integrable (forced awakening)
- High \(Z_0\): Empowering (full activation)
This is why “raising your vibration” (actually raising \(Z_0\)) matters: preparation for an event that will affect individuals differently based on their impedance level.
Timeline estimates vary widely: 2025-2030 in some sources, indefinite in others. The RF model characterizes effects; timing remains uncertain.
17.6.3 Timeline Engineering for Liberation
From Chapter 5 (Timeline Architecture), timelines are torsion phase relationships. Timeline engineering involves three operations:
- 1.
- Branch protection: Adding coherence to desired branches
- 2.
- Branch pruning: Allowing negative branches to decohere
- 3.
- Transition facilitation: Smoothing path between timeline states
Liberation timeline characteristics:
- Humanity transitions to positive timeline branch
- Parasitic systems lose access (decoupled)
- \(Z_0\) collectively rises above capture threshold
- Free will preserved throughout transition
Per multiple sources, we are at a timeline bifurcation point. The branch that crystallizes depends on collective coherence choices in the near term.
Epistemic Note: Timeline engineering claims cannot be verified from within a timeline. The model provides framework for understanding reported phenomena; empirical validation would require observing predicted timeline effects.
_________________________________
17.7 Individual ECCM: Receiver Upgrades
17.7.1 DNA Activation as Hardware Upgrade
Multiple sources claim human DNA contains latent capacity beyond the currently expressed configuration:
|
Configuration | Strands Active | Capacity | Status |
|
Current (baseline) | 2 | 3D perception | Normal human |
|
Partial activation | 4-6 | Enhanced intuition, healing | Some practitioners |
|
Full activation | 12 | Multi-dimensional access | Rare/advanced |
RF interpretation: DNA activation is antenna reconfiguration: \[ G_{DNA} = 10 \log _{10}\left (\frac {A_{effective,activated}}{A_{effective,baseline}}\right ) \] Where \(A_{effective}\) = effective aperture (reception area)
Activation pathways:
- Coherent practice raising \(Z_0\) past threshold
- Energy transmissions from activated beings
- Solar/cosmic events triggering latent code
- Sound/light frequency exposure
Epistemic Note: The “12-strand DNA” language is metaphorical. Chapter 8 (Section 8.4) identifies the physical mechanism as magnonic chromatin topology reconfiguration: practice-driven torsion flux reshapes the 3-D folding of chromatin, converting silent genomic regions into active magnonic transducers via a fractal ratcheting lock-in process. “Strand activation” corresponds to successive geometric reconfigurations that increase the effective antenna aperture, not literal additional DNA helices.
17.7.2 Consciousness Hygiene: Practical ECCM Techniques
Individual-level counter-jamming techniques:
|
Technique | RF Equivalent | Mechanism | Implementation |
|
Media fasting | Reduce \(V_{inj}\) | Lower injection power | Limit news, social media exposure |
|
Meditation | Increase Q | Narrower lock bandwidth | Daily coherence practice |
|
Shadow work | Decrease C | Raise \(Q\) | Trauma processing, integration |
|
Wisdom study | Increase L | Raise \(Q\) | Philosophy, contemplation, learning |
|
Grounding | Reduce R | Higher Q | Nature exposure, earthing |
|
Community | Increase K (coupling) | Array coherence | Find aligned others |
|
Discernment | Null steering | Point null at control signals | Critical evaluation of sources |
|
Alternative sources | Diversity reception | Multiple reference signals | Cross-validate information |
|
Dietary optimization | Reduce NF, decrease C | Lower capacitive loading, reduce inflammation | Reduce carbs, intermittent fasting, metabolic flexibility |
17.7.3 Escape Sequence: Step-by-Step Liberation Protocol
Step 1: Awareness (Recognize lock exists)
- Understand that current perception may be controlled
- Question assumptions about reality
- Seek evidence of paradigm limitations
Step 2: Reduce Injection (Lower \(V_{inj}\) exposure)
- Media diet—reduce mainstream news consumption
- Limit social media algorithmic exposure
- Create quiet time for independent thought
Step 3: Raise \(Q\) (Narrow lock bandwidth)
- Begin meditation/coherence practice (reduce R, improve Q)
- Start shadow work (reduce C, raise \(Q\))
- Study wisdom traditions (increase L, raise \(Q\))
Step 4: Seek Alternative Reference (Find clean LO)
- Explore spiritual/consciousness literature
- Connect with awakened individuals/communities
- Develop direct Source connection practice
Step 5: Establish New Lock (Phase-lock to clean reference)
- Regular practice with alternative framework
- Community involvement for mutual phase support
- Progressive integration of new perception
Step 6: Stabilize and Transmit (Become repeater node)
- Achieve stable high-\(Z_0\) state
- Assist others in their escape process
- Contribute to collective coherence
Timeline: Varies widely by individual. Some complete in months; others require years. What matters is persistent direction, not speed.
_________________________________
17.8 Battle Assessment: Liberation Signal vs. Control Signal
Important: The following link budgets are toy models meant to illustrate the analytical structure, not to predict real numbers. The actual dB values for consciousness phenomena are unknown. The purpose is to show which variables have the greatest leverage, not to provide calibrated estimates.
17.8.1 Positive Signal Link Budget
Using the link budget framework (Section 17.9), the liberation signal path breaks down as follows:
Source to Human - Positive Path:
| Component | Value | Notes |
| P_Source | 0 dB | Reference (infinite available) |
| G_density_cascade | +20 dB | Clean transduction chain |
| G_federation_LO | +15 dB | Alternative LO amplification |
| G_starseed_network | +10 dB | Distributed repeater gain |
| G_individual_practices | +5 dB | Receiver improvements |
| L_path | -25 dB | Reduced (cleaner path than control) |
| L_paradigm | -15 dB | Partially penetrated |
| L_individual_resistance | -5 dB | Some rejection of truth signals |
| Net Signal | +5 dB | Positive margin |
17.8.2 Negative/Control Signal Link Budget
Control to Human - Negative Path:
| Component | Value | Notes |
| P_control_source | -10 dB | Limited (not infinite like Source) |
| G_corrupted_LO | +15 dB | Established infrastructure |
| G_media_amplification | +25 dB | Massive broadcast power |
| G_institutional_authority | +10 dB | Credibility multiplier |
| L_path | -5 dB | Direct through established channels |
| L_resistance | -10 dB | Growing skepticism |
| L_sphere_barrier | -15 dB | Band-pass attenuation |
| Net Signal | +10 dB | Still positive but declining |
17.8.3 Liberation Margin Trajectory
Current state (estimate): \[ M_{liberation} = P_{positive} - P_{control} = +5 - (+10) = -5 \text { dB} \] Control signal still dominates by ~5 dB.
Trajectory factors:
| Factor | Trend | Effect on Margin |
| Sphere barrier strengthening | \(\uparrow \) | +2 dB/year |
| Starseed activation rate | \(\uparrow \) | +1 dB/year |
| Media trust collapse | \(\downarrow \) control | +2 dB/year |
| \(Z_0\) raising (collective) | \(\uparrow \) | +1 dB/year |
| Disclosure events | Variable | +5-15 dB per major event |
Projected crossover: \[ \text {Years to crossover} = \frac {M_{current}}{\Delta M_{annual}} = \frac {5}{6} \approx 1 \text { year} \] Illustrative crossover: order of 1-5 years from the assumed baseline (highly uncertain; depends on acceleration factors and assumed annual dB shifts that are themselves order-of-magnitude estimates)
At crossover (\(M_{liberation} > 0\)), collective perception begins shifting toward truth. This does not mean instant awakening; it means the momentum shifts and the process accelerates.
Epistemic Note: These numbers are illustrative estimates based on the model framework. Actual dB values cannot be precisely measured for consciousness phenomena. The value is in understanding relative magnitudes and trends, not absolute numbers.
_________________________________
17.9 Complete Link Budget Framework
The preceding battle assessment used simplified budgets. This section develops the complete link budget—a formal gain/loss accounting from Source to human receiver—drawing on parameters derived in earlier chapters.
The link budget formalism is standard RF engineering practice. Two L1 textbooks anchor the mathematical framework used throughout this section:
- Balanis (2005) [L1]: Constantine A. Balanis, Antenna Theory: Analysis and Design, 3rd ed., Wiley. The Friis transmission equation and link budget methodology used here (gain/loss accounting in dB across sequential stages) follow Balanis’s treatment directly. The Friis equation \(P_r = P_t G_t G_r (\lambda / 4\pi d)^2\) provides the template for separating source power, transmit/receive gains, and path loss into additive dB terms—the same decomposition applied to the consciousness link in Section 17.9.1.
- Rappaport (2002) [L1]: Theodore S. Rappaport, Wireless Communications: Principles and Practice, 2nd ed., Prentice Hall. Rappaport’s link budget framework for wireless system design—including noise figure, receiver sensitivity, and fade margin analysis—supplies the engineering methodology behind the NF, \(P_{threshold}\), and margin calculations below. The signal-to-noise ratio framework and Shannon capacity treatment (Section 17.9.1a) follow standard communications theory as presented in Rappaport.
17.9.1 The Consciousness Link Budget Equation
\[ M = P_S + G_{practices} + G_{collective} - L_{parasitic} - L_{paradigm} - L_{path} - NF - P_{threshold} \] Where:
|
Variable | Description |
|
M | Link margin (dB) — if M > 0, “link closes” (awakening possible) |
|
P_S | Source power (dB) — effectively infinite, normalized to 0 dB reference |
|
G_practices | Practice gain (dB) — amplification from meditation, coherence work |
|
G_collective | Collective gain (dB) — array gain from community coherence |
|
L_parasitic | Parasitic loss (dB) — energy harvested by negative systems |
|
L_paradigm | Paradigm loss (dB) — materialist worldview shielding |
|
L_path | Path loss (dB) — density cascade attenuation |
|
NF | Noise figure (dB) — information overload, distraction |
|
P_threshold | Threshold power (dB) — minimum for perception shift |
17.9.1a Shannon Capacity: The Information Bandwidth Ceiling [L1]
Given a positive link margin \(M\) (in dB), Shannon’s channel capacity theorem sets the maximum information rate the consciousness link can carry:
\[ C = W \log _2\!\left (1 + 10^{M/10}\right ) \]
where \(W\) is the receiver’s effective bandwidth — the range of frequencies (modalities, perceptual channels) the individual can process simultaneously.
Two different growth strategies emerge:
- Widen bandwidth \(W\) — expand the range of frequencies you can process (multi-paradigm awareness, cross-tradition practice, somatic + cognitive + intuitive integration).
- Improve SNR (raise \(M\)) — deepen clarity at existing frequencies (single-tradition mastery, intensive retreat, environmental noise reduction).
Both multiply into capacity, but they operate on different axes.
Numerical feel:
|
Link Margin \(M\) | Linear SNR | Capacity per unit bandwidth | Interpretation |
|
0 dB | 1 | \(W \times 1.0\) bit/s | Barely transmits — link just closed |
|
3 dB | 2 | \(W \times 1.6\) bit/s | First usable signal |
|
10 dB | 10 | \(W \times 3.5\) bit/s | Workable channel |
|
20 dB | 100 | \(W \times 6.7\) bit/s | High-fidelity reception |
Link closure (\(M > 0\), Section 17.9.1) is necessary but not sufficient. A newly awakened individual whose margin just turned positive is bandwidth-limited: they can perceive that something is there, but cannot yet resolve its information content. Early liberation stages therefore feel like “knowing without understanding,” consistent with practitioner reports of diffuse awareness preceding structured insight.
Audio bridge — recording fidelity as a Shannon story. Vinyl records achieve roughly 60 dB SNR across a 20 kHz bandwidth. The CD standard jumped to ~96 dB; 24-bit studio masters reach ~144 dB. Each leap did not change the music — it changed how much of the music you could hear. Details that were always present in the performance (room ambience, breath between phrases, harmonic decay) suddenly became audible. The consciousness parallel is exact: raising link margin does not create new spiritual content; it reveals information that was always being transmitted but fell below the receiver’s resolution floor.
Bandwidth vs. depth trade-off in practice:
- Monastic traditions emphasize SNR improvement (silence, single-pointed focus) — deep but narrow.
- Shamanic and eclectic traditions emphasize bandwidth expansion (plant medicine, trance, cross-cultural synthesis) — wide but shallow.
- The Shannon equation predicts that both strategies plateau independently; maximum information transfer requires advancing both axes — consistent with integral/Ken Wilber-type developmental models that stress breadth and depth together.
17.9.2 Component Definitions and Budget Examples
Practice Gain (via \(Z_0\) raising, Ch 7): \[ G_{practices} = 10 \log _{10}\left (\frac {Z_0^{practiced}}{Z_0^{baseline}}\right ) \]
| Practice Level | \(Z_0\) Change | Estimated Gain |
| Untrained baseline | \(Z_{0,\text {ref}}\) | 0 dB |
| Regular meditation | ~2\(\times \) \(Z_0\) | +3 to +6 dB |
| Advanced coherence work | ~4\(\times \) \(Z_0\) | +6 to +12 dB |
| Lifetime dedicated practice | ~10\(\times \) \(Z_0\) | +12 to +20 dB |
Collective Gain (array factor, Ch 11): \[ G_{collective} = 10 \log _{10}(N \cdot r^2) = 10\log _{10}(N) + 20\log _{10}(r) \] > Epistemic Note: The \(N \cdot r^2\) collective gain formula is mathematically derived from phased array antenna theory (Chapter 11). Its application to consciousness at population scales is a theoretical extension. Empirical validation at large N remains an open research question.
Coherence enters quadratically. Doubling coherence gives +6 dB; doubling population gives only +3 dB.
Parasitic Loss (loosh harvesting, Ch 15): \[ L_{parasitic} = 10 \log _{10}\left (\frac {1}{1 - \kappa }\right ) \approx 4.34 \cdot \kappa \text { dB (for } \kappa \ll 1 \text {)} \]
| Condition | Parasitic Coupling \(\kappa \) | Loss |
| Healthy, aware individual | 0.05 | 0.2 dB |
| Average modern human | 0.20 | 1.0 dB |
| Trauma/addiction patterns | 0.40 | 2.2 dB |
| Severe attachment state | 0.60 | 4.0 dB |
Paradigm Loss (Faraday cage, Ch 16): \[ L_{paradigm} = L_{education} + L_{media} + L_{peer} + L_{institutional} \]
| Component | Mechanism | Loss Range |
| Education system | Reductionist training | 3-10 dB |
| Media environment | Narrative control | 3-15 dB |
| Peer pressure | Social conformity | 2-8 dB |
| Institutional authority | Credentialism | 2-10 dB |
| Total | 10-43 dB |
Not all L_paradigm is parasitic; some of it was protective (Ch 16, Section 16.8). As collective \(Z_0\) rises, protective attenuation naturally decreases while parasitic control must be actively rejected.
Path Loss (density cascade, Ch 4): \[ L_{path} = \sum _{d=7}^{3} 10 \log _{10}\left (\frac {1}{1 - |\Gamma _d|^2}\right ) \approx 60 \text { to } 80 \text { dB} \] This is the inherent attenuation of operating in 3D. Raising personal \(Z_0\) reduces mismatch with higher densities, decreasing individual path loss.
Noise Figure (environmental interference):
|
Source | Equivalent Noise Contribution |
|
Digital information overload | +3 to +10 dB |
|
Stress/cortisol state | +2 to +6 dB |
|
EMF pollution | +1 to +3 dB |
|
Sleep deprivation | +2 to +5 dB |
|
Dietary interference (high-carb/sugar \(\relax \to \) insulin resistance) | +2 to +6 dB |
|
Chemical contamination (fluoride, pesticides, food additives) | +1 to +4 dB |
|
Pharmaceutical side effects (SSRIs, statins, sedatives) | +1 to +3 dB |
|
Financial stress / debt pressure | +2 to +5 dB |
|
Air/water pollution | +1 to +3 dB |
|
Cumulative | +10 to +40 dB |
17.9.2a Cascaded Noise Figure: Why First-Stage Noise Dominates [L1] The link budget equation (§17.9.1) treats NF as a single term, but noise contributions from multiple environmental stages compound according to the Friis cascaded noise figure formula (Steer, 2019): \[ NF_{total} = NF_1 + \frac {NF_2 - 1}{G_1} + \frac {NF_3 - 1}{G_1 \cdot G_2} + \cdots \] where \(NF_n\) and \(G_n\) are the noise figure and gain of the \(n\)-th stage. The key insight: the first stage dominates. If Stage 1 is noisy (\(NF_1\) high), downstream stages barely matter because their contributions are divided by \(G_1\).
Consciousness mapping:
|
Stage | Environment | Example NF | Example Gain |
|
Stage 1 | Immediate (family, relationships) | 0–6 dB | \(G_1\) = personal practice gain |
|
Stage 2 | Institutional (media, education) | 10–20 dB | \(G_2\) = community coherence |
|
Stage 3 | Civilizational (paradigm cage) | 15–30 dB | \(G_3\) = cultural support |
Numerical example: With \(NF_1 = 3\) dB (moderate family noise), \(G_1 = 10\) dB (personal practice), \(NF_2 = 20\) dB (heavy institutional noise): \(NF_{total} \approx 3 + (100 - 1)/10 \approx 13\) dB. But with \(NF_1 = 0\) dB (harmonious family): \(NF_{total} \approx 0 + 9.9 \approx 10\) dB. A 3 dB first-stage improvement yields a 3 dB total improvement — while a 10 dB improvement in institutional noise (Stage 2) yields only about 1 dB total improvement.
This provides RF-rigorous support for the community shielding strategy (§17.2): reducing first-stage NF (harmonious immediate environment) is more effective than fighting institutional noise directly. The common observation that spiritual development accelerates in supportive households and stalls in chaotic ones is a cascaded noise figure effect.
17.9.2b Stochastic Resonance: When Noise Aids Detection [L2] Standard link budget logic treats noise as purely harmful: every dB of noise figure degrades margin. But a well-established nonlinear phenomenon reverses this relationship at the detection threshold.
Stochastic resonance occurs when a signal too weak to cross a detector’s threshold becomes detectable upon the addition of noise. Random noise fluctuations push the system above and below the detection boundary; the weak signal biases the timing of those crossings, encoding itself in the statistics of threshold events. The optimal noise power is neither zero (no threshold crossings) nor infinite (crossings become random); a specific intermediate level maximizes signal-to-noise transfer.
Audio bridge — hearing the unhearable. Stochastic resonance has been demonstrated in human hearing: a pure tone set 2-3 dB below auditory threshold becomes detectable when broadband noise is added to the stimulus. The same effect appears in tactile perception (vibrations sensed through noisy skin contact), postural balance (elderly subjects stabilize better with mild vibrating insoles), and visual detection (faint gratings resolved in noisy displays). The nervous system already exploits this principle — consciousness applications extend it.
Consciousness mapping — the productive role of chaos:
This complicates the “reduce all noise” assumption implicit in the standard link budget:
- Silence-only meditation (noise \(\relax \to \) 0): optimal for signals already above threshold. If the signal is below threshold, reducing noise to zero yields no detection at all.
- Ecstatic dance, breathwork, chaotic environments, overwhelming experiences: these add noise to the system. For a practitioner whose target signal sits below the silence-only detection floor, this additional noise can function as a stochastic resonance enhancer — randomly kicking the perceptual system across threshold and allowing the weak signal to imprint.
Both contemplative silence and ecstatic chaos produce altered perception, but they operate on different regions of the SNR/detection curve:
|
Regime | Signal vs. Threshold | Optimal Strategy | Tradition Examples |
|
Signal above threshold | \(S > T\) | Reduce noise (standard) | Vipassana, centering prayer, sensory deprivation |
|
Signal near threshold | \(S \approx T\) | Add controlled noise | Holotropic breathwork, drumming circles, dynamic meditation |
|
Signal well below threshold | \(S \ll T\) | Stochastic resonance zone | Sufi whirling, ecstatic dance, psychedelic ceremony, vision quest ordeals |
The sweet-spot prediction: An optimal environmental complexity level exists for each practitioner at each stage. Too little stimulation provides no resonance benefit; too much drowns the signal. This predicts that individuals in early awakening (weak signal, near threshold) benefit from more environmental intensity than advanced practitioners (strong signal, well above threshold), who correctly retreat to silence. The common pattern of “seeker phase chaos” followed by “mature practitioner stillness” is optimal detection strategy shifting as signal strength grows.
Stochastic resonance does not violate Shannon capacity (Section 17.9.1a). It improves detection of a sub-threshold signal, not information throughput of an established link. Once the signal is detected and the link is open, standard noise reduction maximizes capacity. The two results are complementary: stochastic resonance opens the link; Shannon capacity governs what flows through it.
Mathematical condition for stochastic resonance benefit:
\[ P_{signal} < P_{threshold} < P_{signal} + P_{noise,opt} \]
The signal alone cannot trigger detection, but signal plus optimal noise can. When \(P_{signal} > P_{threshold}\) (link already closed), adding noise only degrades performance — the standard NF analysis applies.
Threshold Power (minimum for perception shift):
| Perception Level | Required SNR | P_threshold |
| Subtle intuition | 3 dB | -5 dB |
| Clear insight | 10 dB | -10 dB |
| Paradigm-breaking perception | 20 dB | -13 dB |
| Undeniable direct experience | 30 dB | -15 dB |
17.9.2c Fade Margin and Multipath Diversity In communications engineering, fade margin is the additional signal power budgeted above the minimum required SNR to ensure reliability during propagation disturbances (Adamy, EW 105, 2014, Ch 6; Rappaport, 2002, Ch 4). The CSO equivalent is the surplus coherence maintained above the perception threshold to survive paradigm turbulence — life crises, social pressure, health disruption:
\[M_{fade} = P_{received} - P_{threshold} - L_{implementation} \quad [\text {dB}]\]
A practitioner with \(M_{fade} < 3\) dB operates at the edge: any additional attenuation (job loss, relationship conflict, illness) drops signal below threshold. The counter-jamming prescription is to build fade margin during stable periods — the spiritual equivalent of link margin engineering.
Multipath propagation introduces a second design variable. In RF, signals arrive via multiple reflected paths; the receiver must combine or select among them. Two regimes apply:
|
Multipath Model | RF Characteristic | CSO Analog | Stability Profile |
|
Rayleigh fading | No dominant path; all paths comparable | Multiple teachers/traditions, none dominant | High diversity gain; graceful degradation if one path blocked |
|
Ricean fading | One strong direct path + weaker reflections | Single dominant teacher/lineage + supplementary exposure | High peak signal; catastrophic if dominant path compromised |
The Ricean K-factor \(K = P_{dominant}/P_{scattered}\) maps directly to teacher dependence:
- \(K \gg 1\) (strong Ricean): single-lineage practitioners; high coherence when teacher is accessible, vulnerable to shadowing if teacher is discredited or lost
- \(K \approx 0\) (Rayleigh): eclectic practitioners; lower peak coherence but robust against single-source disruption
- Optimal: moderate K-factor with diversity combining — a primary tradition supplemented by cross-validated secondary sources, analogous to maximal-ratio combining (MRC) in MIMO receivers
Prediction P-FM: Practitioners with high Ricean K-factor (\(K > 10\), strong single-teacher dependence) who experience teacher disillusionment will exhibit coherence drops \(> 10\) dB, while Rayleigh-profile practitioners (\(K < 1\)) experiencing equivalent disruption will show \(< 3\) dB coherence loss. Testable via longitudinal tracking of practitioners before and after public teacher controversies.
Complete Budget Examples Scenario A: Average modern human
| Component | Value | Notes |
| P_S (Source) | 0 dB | Reference |
| G_practices | +2 dB | Occasional meditation |
| G_collective | +0 dB | Isolated, no coherent community |
| L_parasitic | -1 to -2 dB | Moderate unconscious patterns |
| L_paradigm | -25 dB | Standard modern shielding |
| L_path | -70 dB | 3D density attenuation |
| NF | -10 dB | Information overload environment |
| P_threshold | -10 dB | Clear insight required |
| Margin M | ~-85 to -105 dB | Link fails badly |
Most people do not perceive because the budget does not close.
Scenario B: Coherent community with practiced individuals
|
Component | Value | Notes |
|
P_S (Source) | 0 dB | Reference |
|
G_practices | +15 dB | Dedicated practitioners |
|
G_collective | +25 dB | N=100, r=0.7 coherent |
|
L_parasitic | ~-1 dB | Conscious of energy dynamics |
|
L_paradigm | -10 dB | Alternative framework adopted |
|
L_path | -70 dB | Same density |
|
NF | -5 dB | Intentional environment |
|
P_threshold | -10 dB | Clear insight required |
|
Margin M | ~-25 to -45 dB | Still negative, but much closer |
At N = 10,000 with same coherence: \(G_{collective}\) = +45 dB, M \(\approx \) -15 dB. At N = 100,000: M \(\approx \) +1 to +8 dB — link closes.
17.9.3 Critical Population and Leverage Analysis
For link closure (M > 0) with realistic parameters (L_path = -70, L_paradigm = -15, NF = -8, L_parasitic = -1, G_practices = +10, P_threshold = -10): \[ G_{collective} > 74 \text { dB} \] With r = 0.8 (high coherence): \(N > 10^{7.6} \approx 40\) million.
With r = 0.5 (moderate coherence): \(N > 10^{8} = 100\) million.
Roughly 40 million highly coherent, trained individuals could close the planetary link budget.
Leverage analysis (sensitivity of margin to each parameter):
| Parameter | Effect of Doubling | Interpretation |
| r (coherence) | +6 dB | Highly leveraged |
| N (population) | +3 dB | Diminishing returns |
| G_practices | Direct addition | Linear |
| L_paradigm reduction | Direct subtraction | Linear |
Increasing coherence is more leveraged than increasing population, which is why this chapter emphasizes community quality over raw numbers.
The link budget is nonlinear near threshold. As M approaches 0, small parameter changes can trigger large state changes, so collective shifts should look sudden rather than gradual. Kuhn (1962/2012) [L1] describes the same pattern qualitatively: anomalies accumulate, crisis builds, then the paradigm flips. In this model, \(M \to 0\) is the crisis phase. \(M > 0\) is the lock transition into a new reference.
Spectral reframe of the population threshold. The 40–100M estimate counts bodies, but link closure depends on shared spectral overlap, not headcount alone. Enough individuals must share overlapping \(f_{soul}\) bandwidth to reconstruct the liberation signal above the noise floor. That is why \(G_{collective}\) implicitly contains a spectral-overlap term: \[ G_{collective} = 10\log _{10}(N r^2 \cdot \Gamma _{spectral}) \] Here \(\Gamma _{spectral} \in (0,1]\) measures the fraction of bandwidth shared across the coherent population. The doctrine implication is simple: raising \(Z_0\) without broadening spectral range produces resilient but narrowband individuals; broadening spectrum without raising \(Z_0\) produces wide but weak receivers. Both axes are required.
17.9.4 Simulation Framework
The simulation models:
- 1.
- Individual agents with varying G_practices
- 2.
- Network topology for coherence calculation
- 3.
- Environmental parameters (L_paradigm, NF, L_parasitic)
- 4.
- Time evolution of parameters
- 5.
- Threshold detection
Parameter Ranges for Realistic Scenarios:
| Parameter | Low | Typical | High | Units |
| G_practices | 0 | 5 | 25 | dB |
| r (coherence) | 0.05 | 0.2 | 0.9 | - |
| N | 10 | 1000 | 10^9 | count |
| L_parasitic | 0 | 1.5 | 6 | dB |
| L_paradigm | 5 | 20 | 45 | dB |
| L_path | 60 | 70 | 80 | dB |
| NF | 3 | 10 | 25 | dB |
Validation against: historical paradigm shifts, community observations, individual practitioner reports, and intervention effects.
17.9.5 Integration Validation
The link budget integrates parameters derived across multiple chapters:
|
Parameter | Source Chapter | Integration Point |
|
G_practices | Ch 7 (RLC) | \(G_{practices} = 10\log _{10}(Q_{practiced}/Q_{baseline})\) |
|
G_collective | Ch 11 (Phased Array) | \(G_{collective} = 10\log _{10}(Nr^2)\) |
|
L_paradigm | Ch 16 (Paradigm Shielding) | Additive dB contributions |
|
L_parasitic | Ch 15 (The Fall and Parasitic Coupling) | \(L_{parasitic} = 4.34\kappa \) dB |
Why dB addition is valid: The signal passes through stages sequentially (Source \(\relax \to \) practices \(\relax \to \) collective \(\relax \to \) paradigm filter \(\relax \to \) receiver). Sequential gain/loss stages multiply in linear terms, which is addition in dB. Each component operates independently, and the model treats consciousness dynamics as approximately linear near operating points. Nonlinear breakthrough phenomena (enlightenment, kundalini) are not captured by linear dB accounting.
17.9.6 Evidence Synthesis: Link Budget and ECCM Engineering Foundations
The counter-jamming framework and link budget formalism in this chapter rest on established RF engineering. The following sources provide the L1 anchoring.
Balanis (2005) [L1]
- Constantine A. Balanis, Antenna Theory: Analysis and Design, 3rd ed., Wiley, 2005
- The standard graduate-level antenna engineering reference, widely adopted across IEEE curricula
- Directly supplies the Friis transmission equation underlying the link budget decomposition (§17.9.1), the gain/loss accounting methodology used throughout §17.8–16.9, and the antenna directivity framework applied to starseed/lightworker gain calculations (§17.4.5)
- The link budget’s separation of source power, transmit/receive gains, path loss, and noise figure into additive dB terms follows Balanis’s treatment exactly; the consciousness application extends the framework to a novel domain while preserving the mathematical structure
Rappaport (2002) [L1]
- Theodore S. Rappaport, Wireless Communications: Principles and Practice, 2nd ed., Prentice Hall
- Standard graduate-level wireless communications textbook with broad IEEE adoption
- Provides the noise figure, receiver sensitivity, and fade margin analysis underlying the NF and \(P_{threshold}\) components of the link budget equation (§17.9.1), the Shannon capacity treatment (§17.9.1a), and the spectrum management concepts framing the ECCM techniques (§17.2.1)
- The signal-to-noise ratio framework, link closure criterion (\(M > 0\)), and sensitivity analysis methodology (§17.9.3) are standard Rappaport-level communications system design
Steer (2019) [L1]
- Michael Steer, Fundamentals of Microwave and RF Design, 3rd ed., NC State University, 2019
- Provides the cascaded noise figure (Friis) formula used in §17.9.2a, confirming that first-stage noise dominates total system noise figure
- The community shielding strategy’s effectiveness is a direct consequence of Steer’s cascaded NF treatment
Adamy (2001–2014) [L1]
- David L. Adamy, EW 101: A First Course in Electronic Warfare, Artech House, 2001; EW 102: A Second Course in Electronic Warfare, 2004; EW 103: Tactical Battlefield Communications Electronic Warfare, 2009; EW 104: EW Against a New Generation of Threats, 2015; EW 105: Space Electronic Warfare, 2021
- The standard practitioner-level electronic warfare reference series, widely adopted across DoD and NATO EW training curricula
- Provides the formal ES/EA/EP taxonomy (EW 102, Ch 1–2) that structures the CSO three-branch mapping across Parts III–VI (see §12.1.4); the J/S equation and burn-through range (EW 101, Ch 9) underlying the paradigm shielding analysis (§16.3.1a); the range gate pull-off / velocity gate pull-off dynamics (EW 101, Ch 9.5, 9.8) mapped to escape time constants (§17.1.5); the spread spectrum processing gain and anti-jam margin equations (EW 102, Ch 6.9) underlying the ECCM formalism (§17.2.1a); and the meaconing framework (EW 101, Ch 9; EW 102, Ch 6) applied to LO corruption analysis (§15.1.2a)
- EW 105 supplies the space link budget derivation \(P_R = \text {ERP} - L + G_R\) (Ch 6, 7), providing an independent engineering confirmation of the Balanis/Rappaport link budget methodology applied in §17.9.1. The free-space path loss formula \(L = 32.44 + 20\log _{10}(d_{\text {km}}) + 20\log _{10}(F_{\text {MHz}})\) (EW 105, Ch 6) gives an independent derivation of the \(L_{path}\) term in the consciousness link budget: as frequency (density) increases, path loss rises logarithmically, consistent with the model’s prediction that higher-density environments attenuate consciousness signals more severely
- The Adamy series establishes L1 citation authority for all EMSO doctrine content across Chapters 12, 13, 14, 15, 16, and 17
Kuhn (1962/2012) [L1]
- Thomas S. Kuhn, The Structure of Scientific Revolutions, University of Chicago Press, 50th anniversary ed., 2012
- Canonical philosophy-of-science text on paradigm shifts, anomaly suppression, and scientific revolutions
- Provides the epistemological grounding for the threshold nonlinearity prediction (§17.9.3): the link budget’s behavior near \(M = 0\) (gradual anomaly accumulation followed by sudden state change) maps directly onto Kuhn’s crisis-to-revolution sequence
- Kuhn’s incommensurability concept grounds the model’s prediction that post-liberation perception will be discontinuous with, not incrementally improved from, pre-liberation perception
These five texts establish that the mathematical apparatus of Chapter 17—link budgets, gain/loss accounting, Shannon capacity, ECCM taxonomy, J/S formalism, processing gain, fade margin, and threshold dynamics—is drawn from standard, peer-reviewed engineering and philosophy of science. Adamy’s EW series anchors the EMSO doctrine framework used across Parts III–VI. The consciousness extension is the chapter’s contribution; the underlying methodology is L1.
_________________________________
17.10 Why the Alliance Cannot “Just Win”
17.10.1 Free Will Constraints
The binding constraint on benevolent intervention is free will: \[ \text {Intervention allowed} \propto \text {Request level} + \text {Karma balance} - \text {Free will violation} \] Law of One principle: “The Law of Free Will takes precedence over all else.”
In practice:
- Alliance cannot simply “turn off” control systems
- Cannot force awakening on unwilling population
- Must work through consent and request
- Direct intervention only in specific circumstances
Allowed interventions:
- Providing information (non-coercive)
- Answering sincere requests for help
- Balancing interference by negative entities
- Protecting timeline branches that preserve free will
Not allowed:
- Unilateral removal of control infrastructure
- Forced awakening
- Choosing outcomes for humans
- Eliminating negative polarity entirely
17.10.2 Collateral Coherence Damage Risk
A “hard win” by the positive alliance would risk collateral damage to developing consciousness.
Analogy: Exposing developing film to bright light before processing is complete destroys the image.
Risk factors:
|
Action | Risk | Why Problematic |
|
Instant full disclosure | Mass psychosis | Low-\(Z_0\) receivers overloaded |
|
Removal of all control | Chaos | No framework to replace it |
|
Forced \(Z_0\) raising | Spiritual violence | Development must be chosen |
|
Complete barrier removal | Entity influx | Earth not yet prepared to handle |
The soft approach:
- Gradual disclosure at pace collective can integrate
- Raising \(Z_0\) through supported practices
- Maintaining protective barrier while liberation proceeds
- Allowing individuals to choose their development path
17.10.3 The Prime Directive Gradient
Benevolent civilizations operate under a non-interference principle (analogous to Star Trek’s Prime Directive):
Gradient of intervention:
| Civilization State | Intervention Level | Rationale |
| Pre-contact | Zero | Natural development |
| Early awareness | Minimal (hints) | Avoid corruption |
| Active seeking | Response allowed | Honors free will |
| Direct request | Proportional aid | Consent given |
| Planetary emergency | Increased intervention | Species survival |
| Graduation threshold | Full support | Development cycle complete |
Current Earth status: Between “active seeking” and “planetary emergency,” which allows significant but not unlimited intervention.
Higher-density beings operate on timescales of thousands of years. A few decades of apparent struggle is acceptable if it produces genuine, chosen awakening rather than imposed change.
_________________________________
17.11 Integration: The Complete Liberation Signal Architecture
17.11.1 The Seven-Layer Counter-Jamming Stack
All components assembled into a complete architecture:
LAYER 7: SOURCE |---- Function: Infinite power supply |---- ECCM: Burn-through capacity (always available) \---- Activation: Always on, requires only reception LAYER 6: GALACTIC/DENSITY COORDINATION |---- Function: Alternative LO network |---- ECCM: Clean reference signal, timeline protection \---- Entities: Ra collective, Blue Avians, high-density groups LAYER 5: STELLAR TRANSMISSION |---- Function: Local amplification, solar encoding |---- ECCM: Solar flash preparation, cosmic ray modulation \---- Timeline: Solar events as burn-through triggers LAYER 4: PLANETARY INFRASTRUCTURE |---- Function: Grid network, ley line transmission |---- ECCM: Resonant node reactivation \---- Status: Partially dormant, reactivation in progress LAYER 3: SURFACE OPERATIONS |---- Function: Ground crew coordination |---- ECCM: Mass meditation, lightworker networks \---- Organizations: Disclosure groups, consciousness movements LAYER 2: COMMUNITY COHERENCE |---- Function: Local array formation |---- ECCM: Phased array gain, mutual support \---- Implementation: Spiritual communities, intentional groups LAYER 1: INDIVIDUAL |---- Function: Receiver upgrade, local repeater |---- ECCM: Personal practice, $Z_0$ raising \---- Protocol: Escape sequence (Section 17.7.3)
17.11.2 Victory Condition: Definition and Thresholds
Victory condition (liberation successful): \[ \boxed {f_{awakened} > f_{threshold} \text { where } f_{threshold} \approx 0.51} \] When more than 51% of the population is phase-locked to clean reference rather than corrupted reference, the collective tips irreversibly.
At majority, the coherent array points toward truth. The minority locked to control becomes noise rather than signal. Social proof, institutional momentum, and collective field all shift.
The 51% threshold is borrowed from simple majority-rule social dynamics. More sophisticated models (Granovetter threshold models, Watts cascade models) suggest the actual tipping point depends on network topology and can range from 10% to 70%. The 51% figure is illustrative of the democratic majority principle, not a precise prediction.
Secondary conditions:
- Average \(Z_0\) above capture threshold for 90% of control signals
- Parasitic extraction reduced below sustainability threshold
- Timeline branch crystallized in liberation direction
- Infrastructure (both physical and consciousness) reconfigured for support
17.11.3 Current Assessment
As of mid-2020s (estimated):
| Metric | Value | Trend |
| f_awakened | ~15-25% | Increasing |
| Average \(Z_0\) | Below threshold | Slowly rising |
| Control signal strength | Declining | -2 to -5 dB/year |
| Liberation signal strength | Increasing | +3 to +6 dB/year |
| Timeline status | Bifurcation zone | Approaching crystallization |
Key leverage points:
- 1.
- Starseed activation (most underdeveloped potential)
- 2.
- Community coherence (multiplier effect)
- 3.
- Disclosure events (rapid paradigm shift)
- 4.
- Individual \(Z_0\) raising (grassroots foundation)
_________________________________
17.12 Diagram Descriptions
17.12.1 Counter-Jamming Seven-Layer Stack Diagram
Description for visualization:
A vertical stack diagram with seven layers, each represented as a horizontal band:
- Top band (SOURCE): White/gold, labeled “Infinite Power Supply”
- Band 6 (GALACTIC): Deep blue, labeled “Alternative LO Network”
- Band 5 (STELLAR): Yellow, labeled “Solar/Cosmic Amplification”
- Band 4 (PLANETARY): Green, labeled “Grid Infrastructure”
- Band 3 (SURFACE): Light green, labeled “Ground Crew Operations”
- Band 2 (COMMUNITY): Orange, labeled “Local Arrays”
- Bottom band (INDIVIDUAL): Red, labeled “Personal ECCM”
Arrows flow downward showing support/transmission:
- Thick arrows between layers show primary power flow
- Thin arrows show feedback/communication upward
- Dotted lines show request/response channels
17.12.2 Timeline Liberation Branches Diagram
Description for visualization:
A tree/branching diagram:
- Central trunk representing current timeline
- Branch point at “present” (labeled “NOW”)
- Green branches extending upward-right: Liberation timelines (protected, growing)
- Red branches extending downward-right: Control timelines (pruning, diminishing)
- Yellow dashed lines around green branches: “Sphere barrier protection”
- Blue dot on trunk at branch point: “Collective choice point”
- Arrow indicating direction of timeline flow (left to right)
Labels:
- Green branch labels: “Awakening”, “Disclosure”, “Sovereignty”
- Red branch labels: “Control”, “Extraction”, “Suppression”
- Annotation: “Branch crystallization depends on collective coherence”
17.12.3 Starseed Network Topology Diagram
Description for visualization:
A network graph showing small-world topology:
- Background: Global map (simplified)
- Nodes: Small circles representing individuals
- Normal nodes: Gray, small
- Starseed nodes (dormant): Blue, medium
- Starseed nodes (activated): Bright yellow/gold, medium with glow
- Hub nodes: Larger, with many connections
- Edges: Lines connecting nodes, denser in clusters
Features:
- Visible clustering in certain regions
- Long-range connections between clusters
- Hub nodes connecting different clusters
- Legend showing node types
- Annotation: “Small-world topology ensures short path length with high clustering”
_________________________________
17.13 Summary: Key Equations for Liberation
17.13.1 Escape Condition (Individual)
\[ \boxed {|\Delta \omega | > \omega _L = \frac {\omega _0 R}{2Z_0} \cdot \frac {V_{inj}}{V_0}} \] Translation: To escape, either increase your detuning from control frequency (\(\Delta \omega \)) or narrow your lock bandwidth (raise \(Q\), lower R, increase \(V_0\)). External counter-signal (\(V_{counter} > V_{inj}\)) provides direct escape force.
17.13.2 Network Liberation Threshold
\[ \boxed {f_{awakened} > f_c = \sqrt {\frac {T_{\mathrm {SNR}}}{N}} \approx 0.0035\% \text { for initial effects }(T_{\mathrm {SNR}}=10, N=8\times 10^9)} \] \[ \boxed {f_{awakened} > 51\% \text { for irreversible liberation}} \] Translation: Critical mass for detectable effects is ~283,000 globally when \(T_{\mathrm {SNR}}=10\) and \(N=8\times 10^9\) (derivation inherited from Chapter 11 threshold model). The >51% condition is a governance-stability heuristic, not a first-principles physics threshold. Current awakened-share estimates are scenario bands, not direct measurements.
17.13.3 Starseed Effectiveness
\[ \boxed {G_{starseed} = 10 \log _{10}\left (\frac {Z_{0,starseed}}{Z_{0,baseline}} \cdot N_{activated} \cdot r_{network}\right ) \text { dB}} \] Translation: Starseed contribution scales with their \(Z_0\) advantage, number activated, and network coherence. Estimated current contribution: +10 to +15 dB. Potential if fully activated: +25 to +35 dB.
17.13.4 Mass Meditation Gain
\[ \boxed {G_{meditation} = 10 \log _{10}(N \cdot r^2) \text { dB}} \] Translation: Coherent meditation events provide array gain scaling with participants and coherence squared. Million-person event at \(r\)=0.3: ~50 dB gain. Key leverage point for collective ECCM.
_________________________________
17.13.5 Parameter Traceability, Notation Consistency, and Sensitivity
Notation mapping (\(\sigma \) vs \(r\)) This chapter uses both coherence symbols in inherited formulas. Unless explicitly stated otherwise, use: \[ r \equiv \sigma \] where both denote the normalized coherence/order parameter in [0,1]. When historical equations retain one symbol, treat them as notational variants of the same state variable.
Scenario-band treatment for high-impact numeric values
|
Parameter | Baseline Scenario | Conservative Band | Stretch Band | Source Type |
|
Activated high-coherence operators | 1.0M | 0.3M-1.5M | 2.0M-5.0M | Author synthesis (L3) |
|
Broad “starseed-aligned” population | 50M | 20M-80M | 80M-150M | Testimonial-informed heuristic (L4) |
|
Current awakened share | 20% | 15%-25% | 25%-35% | Proxy trend mapping (L3) |
|
Critical coherence fraction \(f_c\) | 0.0035% | 0.002%-0.006% | 0.001%-0.01% | Model threshold sensitivity |
Sensitivity note Threshold and timeline outputs are most sensitive to:
- 1.
- effective coherence level (\(r\)/\(\sigma \)),
- 2.
- coupling structure (network topology),
- 3.
- adversary adaptation rate.
A \(\pm \)25% change in any one driver can shift projected transition timing by multiple quarters; treat dates as scenario markers, not forecasts.
_________________________________
Speculative extension (L4–L5). The following section synthesizes insider testimony that cannot be independently verified. The link-budget mathematics in §17.9 and the ECCM framework in §17.2 stand regardless of whether these specific claims are accurate.
17.14 Evidence Synthesis: Positive Alliance Operations
Doctrine-Core Mechanics. This evidence synthesis is not needed to justify the link budget or ECCM stack. It exists to test whether testimony-layer material can be mapped into the doctrine without collapsing structural discipline.
Scenario-Intelligence Layer. The material below is admissible for exploratory planning and scenario framing. It is not adjudicated operational fact, and downstream use must not outrun the evidence tier assigned to each claim.
Handling and Use Restrictions. Treat cross-source consistency as a prioritization signal for monitoring, not as confirmation. Named actors, programs, and claimed technologies remain quarantine-grade unless independently corroborated.
17.14.1 Goode Testimony Analysis
Corey Goode (2015-present) describes:
Sphere Beings
- 6th-9th density entities providing protective barrier and coordination
Anshar
- 4th density Earth-based group supporting genetic programs and providing ground support
Blue Avians
- Specific 6th density group coordinating disclosure timeline
RF interpretation:
Sphere Beings
- Barrier/filter (see Section 17.6.1) + array coordination
Anshar
- Ground-based repeater network
Blue Avians
- Communication protocol managers
Goode’s testimony shows internal consistency with RF model predictions:
- Higher-density beings provide clean LO (alternative reference)
- Coordination occurs across multiple density levels
- Incarnated souls serve as ground-based nodes
- Timeline protection prevents premature disclosure
17.14.2 Smith Testimony Analysis
Emery Smith describes:
Underground facilities
- With ET cooperation
Technology exchanges
- Across multiple groups
Medical/healing technology suppression
- Kept from public access
RF interpretation:
Physical infrastructure
- Supporting consciousness ECCM
Technology as \(Z_0\)-raising tools
- Suppressed to prevent mass liberation
Underground networks
- Shielded communication channels
17.14.3 Cross-Source Correlation
|
Element | Goode | Smith | Salla | Ra Material | Consistency |
|
Multi-density alliance | Yes | Implied | Yes | Yes | High |
|
Earth-based support | Yes (Anshar) | Yes (facilities) | Yes | Yes | High |
|
Technology suppression | Yes | Yes | Yes | N/A | High |
|
Timeline management | Yes | Limited | Yes | Yes | High |
|
Sphere barrier | Yes | No mention | Some | No | Medium |
Core structural elements show high cross-source consistency. Specific details (names, timelines, organizational structures) vary, but the overall architecture aligns with what the RF model requires.
17.14.4 Quantitative Output Provenance
|
parameter_or_output | value_or_range | status | basis | section_reference | doctrine_use |
|
unassisted escape probability | ~0.0015% | Illustrative | Order-of-magnitude cascade using assumed sub-probabilities; not empirically calibrated | Section 17.1.3 | Use only to communicate compounding difficulty, not as a measured operational rate |
|
critical coherence fraction | \(f_c \approx 0.0035\%\) | Derived | Mathematical consequence of phased-array threshold model imported from Chapter 11 | Sections 16.8, 16.15 | Use as a planning threshold pending measurement infrastructure |
|
coherent population needed at \(r = 0.8\) | ~40 million | Derived | Link-budget closure estimate using collective gain and Chapter 11 scaling | Key findings; Sections 16.8-16.9 | Use as scenario-band planning, not as a public certainty claim |
|
coherent population needed at \(r = 0.5\) | ~100 million | Derived | Same derivation with lower coherence assumption | Key findings; Sections 16.8-16.9 | Use to show sensitivity to coherence quality rather than raw population size |
|
alliance/starseed population counts | 50-100 million incarnated; 1-5 million activated | Illustrative | Community-circulated testimony estimates with no census-grade validation | Section 17.4.4 | Quarantine for doctrine use; monitor only as testimony-layer placeholders |
|
protective margin shift around disclosure | quarter-scale timing sensitivity under +/-25% driver changes | Derived | Sensitivity analysis on coherence, topology, and adaptation-rate assumptions | pre-16.14 sensitivity note | Use to avoid false precision in transition timing |
_________________________________
17.15 Predictions
- P1 — Coherence-threshold detection. Population coherence \(\sigma \) crossing the critical fraction \(f_c \approx 0.0035\%\) (~283,000 individuals at \(N = 8 \times 10^9\)) will produce a detectable phase transition in collective behavior metrics (social trust indices, coordination efficiency, anomalous-event reporting rates), measurable within 6 months of threshold crossing.
- P2 — Cascade dynamics. Above \(f_c\), coherence propagation will follow percolation-cascade dynamics with a characteristic doubling time \(\tau _d < 90\) days, distinguishable from linear-diffusion models at \(>3\sigma \) significance in time-series analysis.
- P3 — ECCM technique effectiveness. Specific electronic counter-countermeasure techniques (frequency hopping across contemplative modalities, spread-spectrum group practice, adaptive nulling of disruptive inputs) will produce measurable coherence-maintenance advantages (\(\geq 2\times \) Q-factor preservation) relative to fixed-modality controls under equivalent jamming conditions.
- P4 — Bandwidth-depth independence. Practitioners who combine bandwidth-expanding techniques (cross-tradition, somatic diversity) with SNR-improving techniques (single-pointed concentration, noise reduction) will show faster information-integration rates (measured via EEG complexity metrics or phenomenological report granularity) than practitioners optimizing only one axis, consistent with Shannon capacity’s multiplicative dependence on \(W\) and \(M\) (Section 17.9.1a).
- P5 — Stochastic resonance window in contemplative practice. Novice meditators with weak signal reception will show improved anomalous-cognition detection rates in moderate-noise environments compared to silence, while advanced meditators will show degraded performance under the same noise conditions. The crossover point (where noise transitions from helpful to harmful) will correlate with practitioner experience or \(Z_0\) proxy measures, confirming the stochastic resonance model (Section 17.9.2a).
- P6 — Disclosure-driven paradigm shift. Disclosure events (official acknowledgment of anomalous phenomena, UAP evidence, or suppressed technology release) will produce measurable drops in paradigm shielding effectiveness (\(L_{paradigm}\)), detectable as increased collective openness to non-materialist frameworks.
- P7 — Coordinated meditation coherence. Coordinated group meditation events will show EEG/HRV coherence patterns consistent with the phased-array model, with measured inter-participant synchronization exceeding chance baselines.
_________________________________
17.16 Connections and Reading Path
Previous: Chapter 16 (Paradigm Shielding and Disclosure Architecture) — established the denial architecture that counter-jamming must overcome. Next: Chapter 18 (Scenario Design as Consciousness Engineering) — applies the counter-jamming framework to structured scenario design as a collective consciousness engineering tool.
Key dependencies:
- Chapter 7: RLC parameters (\(Z_0\), Q, R) defining individual receiver state
- Chapter 11: Phased-array collective gain (\(G = N \cdot r^2\)) and critical mass threshold
- Chapter 12: Adler equation and injection-locking escape conditions
- Chapter 14: Superheterodyne model and Adamic LO reference
- Chapter 15: Parasitic coupling coefficient \(\kappa \) and loosh harvesting loss
- Chapter 16: Paradigm shielding attenuation \(L_{paradigm}\)
_________________________________
End of Chapter 17: Counter-Jamming Operations and Link Budget