Chapter 12: Injection Locking and Perception Management
Control Mechanisms and Individual Sovereignty
KEY FINDINGS — Chapter 12: Injection Locking and Perception Management
Evidence-tier key: see front matter for [L1]–[L4] definitions.
- The Adler equation governs belief capture: lock bandwidth \(\propto 1/Q\), so higher quality factor (sovereignty) narrows vulnerability to narrative capture [L1]
- Competing injection model reveals an asymmetry: truth signals closer to natural frequency gain resonant amplification, requiring control signals to compensate with raw power [L1]
- Critical mass for narrative escape is \(f_c \approx \omega _{L,C}/(\omega _{L,C} + K_{mean}) \approx 37.5\%\), consistent with historical cascade evidence (30-40%) from Soviet dissolution, Berlin Wall, and social movements [L1-L2]
- Adaptive beamforming (MVDR/LMS) maps precisely to algorithmic content suppression, with documented platform behavior matching model predictions for adaptation rate and null steering [L1]
- Current population assessment: 30-40% firmly locked, 25-35% questioning, 15-25% unlocked, 5-10% never locked – with lock weakening due to trust collapse and rising network connectivity [L2-L3]
_________________________________
Epistemic note [L1-L3]: This chapter separates established RF dynamics (L1), model-dependent social mappings (L2), and speculative extension claims (L3). Use L1-L2 content for doctrine decisions; treat L3 content as hypothesis overlays requiring independent corroboration and explicit falsification checks.
12.1 RF Analogy Overview
12.1.1 What is Injection Locking?
In RF engineering, injection locking occurs when an oscillator is exposed to an external signal and synchronizes (locks) its frequency to that signal. The oscillator gives up its natural frequency and adopts the injected frequency. The torsion field substrate established in Chapter 0 provides the physical mechanism through which injection locking operates on consciousness.
This is a phase transition. Below a certain injection power, the oscillator maintains its independence. Above that threshold, it locks to the external signal.
Key RF principle: A weak oscillator near a strong transmitter will be captured by the transmitter’s frequency. The oscillator does not “choose” to synchronize; it is compelled by the physics of coupling.
EMSO doctrine. In electronic warfare, injection locking is Electronic Attack (EA) — the deliberate use of a strong transmitted signal to force a target oscillator off its natural frequency and onto the attacker’s (Adamy, EW 102, 2004, Ch 1; see Section 12.1.4 for the full ES/EA/EP taxonomy). The Adler equation quantifies the capture condition: any oscillator within the locking bandwidth \(\Delta \omega _L\) will synchronize regardless of its prior state. This is control through physical law.
Audio bridge. The audio equivalent is sidechain compression: one signal (the “key”) forces another to follow its dynamics. Auto-tune is injection locking of pitch — the algorithm pulls a voice toward the nearest semitone grid whether the singer intended it or not. Binaural beat entrainment works identically: the brain’s oscillatory frequency locks to the externally-imposed beat frequency.
12.1.2 Why This Maps to Belief Dynamics
Each individual is modeled as an oscillator (Chapter 7) with natural frequency \(\omega _0\), quality factor \(Q = Z_0/R\), and characteristic impedance \(Z_0 = \sqrt {L/C}\). External signals (media, institutions, social pressure) attempt to lock individuals to specific belief states. The Adler equation (1946) governs this capture; its lock bandwidth scales as \(\Delta \omega _{lock} \propto 1/Q\), so higher Q means narrower vulnerability. The full formalism is developed in Section 12.2.
The RF injection locking formalism draws on standard graduate-level treatments: Balanis (2005) for antenna engineering and Q-factor foundations, and Rappaport (2002) for modulation theory and spectrum management [L1].
12.1.3 Adaptive Beamforming Overview
Injection locking describes how individual oscillators are captured. Adaptive beamforming describes how control systems manage the collective:
Adaptive beamforming adjusts antenna array weights to maximize signal in desired directions while placing nulls (zeros) toward interference. The array adapts continuously: tracking desired signals, suppressing jammers, responding in real-time.
Perception management is adaptive beamforming of collective consciousness. The control system adjusts weights continuously: amplifying narratives that serve power, nulling information that threatens it.
This section extends the individual injection locking model to the system-level control architecture. The two mechanisms work together: injection locking captures individual oscillators; adaptive beamforming steers the collective array.
12.1.3a Network-Centric Electronic Attack
Classical injection locking assumes a single powerful transmitter overwhelming a single receiver. Modern information control operates differently: networked electronic attack, in which sensing, jamming, and targeting are distributed across many cooperating nodes (Adamy, EW 104, 2015, Ch 1–3).
In network-centric EA, the weapon system is the network itself. Adamy identifies four operational variables that become critical once EA is distributed:
|
Variable | RF Definition | Social Mapping |
|
Latency | Time between target detection and jammer response | Speed of narrative response to breaking events |
|
Authentication | Verification that network nodes are friendly | Bot detection, source credibility, editorial gatekeeping |
|
Fidelity | Accuracy of target parameters passed between nodes | How faithfully a talking point is reproduced across outlets |
|
Node placement | Geometric positioning of distributed jammers | Strategic placement of influencers, platforms, and institutional voices |
Social media constitutes a distributed network-centric EA architecture. No single account or outlet provides decisive injection power; the network of coordinated nodes produces a combined effective radiated power that far exceeds any individual source. The kill chain from event detection to narrative lock operates on timescales of minutes — faster than individual critical evaluation.
Prediction (P-NW): Network-centric EA predicts that coordinated multi-platform narrative campaigns will achieve lock on populations where single-source messaging of equivalent total power would fail, because distributed nodes exploit the authentication gap (individual credibility assessment per-source) while delivering aggregate injection power that exceeds the population’s collective lock bandwidth. [L2]
12.1.4 The ES/EA/EP Taxonomy: CSO Mapping
Electronic warfare doctrine divides the discipline into three branches (Adamy, EW 101, 2001, Ch 1; EW 102, 2004, Ch 1):
Electronic Support (ES) — the receiving part of EW: intercept, identify, and locate sources of electromagnetic energy for threat recognition, targeting, and planning. Formerly ESM (Electronic Support Measures).
Electronic Attack (EA) — the use of electromagnetic energy, directed energy, or antiradiation weapons to attack personnel, facilities, or equipment with the intent of degrading, neutralizing, or destroying enemy combat capability. Formerly ECM (Electronic Countermeasures). Includes jamming, injection locking, deception, and meaconing.
Electronic Protection (EP) — measures taken to protect personnel, facilities, and equipment from any effects of friendly or enemy employment of EW that degrade, neutralize, or destroy friendly combat capability. Formerly ECCM (Electronic Counter-Countermeasures).
— Adamy, EW 102 (2004), Ch 1, p. 3
The CSO framework maps directly onto this taxonomy:
|
EW Branch | CSO Function | Primary Chapters |
|
ES (characterize) | Map the consciousness spectrum environment; identify signal sources, interference, and receiver states | Ch 6 (Signal Environment), Ch 7 (RLC), Ch 14 (Seeder Infrastructure) |
|
EA (deny/attack) | Injection locking, paradigm cage, parasitic coupling, LO corruption | Ch 12 (Injection Locking), Ch 15 (The Fall), Ch 16 (Paradigm Shielding) |
|
EP (protect) | Counter-jamming, \(Z_0\) raising, coherence building, practice protocols | Ch 17 (Counter-Jamming), Ch 18 (Scenario Design), Ch 19 (Spiritual Traditions) |
This mapping is not decorative. Each EMSO doctrine blockquote in the CSO text (Chapters 12, 13, 14, 15, 16, 17) falls within exactly one branch of the ES/EA/EP taxonomy. The taxonomy ensures that the reader knows which kind of spectrum operation is being described at every point, and can distinguish characterization (ES) from attack (EA) from protection (EP) when evaluating any consciousness-domain phenomenon.
_________________________________
12.2 Mathematical Model
12.2.1 Core Dynamics: Single Oscillator
The Adler equation in normalized form: \[ \frac {d\phi }{dt} = \Delta \omega - \omega _L \sin (\phi ) \] Where the locking bandwidth is: \[ \omega _L = \frac {\omega _0}{2Q} \cdot \frac {V_{inj}}{V_0} \] ### 12.2.2 Locking Condition
For stable lock (constant \(\phi \)): \[ \frac {d\phi }{dt} = 0 \implies \sin (\phi ) = \frac {\Delta \omega }{\omega _L} \] This has a solution only when: \[ \left |\Delta \omega \right | \leq \omega _L \] Therefore, the locking range is: \[ \boxed {\Delta \omega _{lock} = \pm \frac {\omega _0}{2Q} \cdot \frac {V_{inj}}{V_0}} \] Physical interpretation:
- Locking range \(\propto \) injection power (\(V_{inj}\))
- Locking range \(\propto \) 1/Q = R/\(Z_0\) (low-Q oscillators are easier to capture)
- Locking range \(\propto \) \(\omega _0\) (faster oscillators have wider locking bands)
12.2.3 Social Mapping of Parameters
|
RF Term | Symbol | Social Mapping | Interpretation |
|
Natural frequency | \(\omega _0\) | Intrinsic belief tuning | Your “native” channel before external influence |
|
Characteristic impedance | \(Z_0 = \sqrt {L/C}\) | Depth of processing | Visible impedance range—determines perceptible density tiers (equivalently: accessible frequency bands) |
|
Quality factor | \(Q = Z_0/R\) | Sovereignty / lock resistance | Primary development measure—harder to capture; Q \(\propto \) \(Z_0\)/R |
|
Injected frequency | \(\omega _{inj}\) | Narrative frequency | The belief state the external signal tries to impose |
|
Frequency offset | \(\Delta \omega \) | Belief distance | How far the narrative is from your natural position |
|
Injection amplitude | \(V_{inj}\) | Media/institutional power | Broadcast strength of narrative source |
|
Oscillator amplitude | \(V_0\) | Individual signal strength | Personal influence, platform, inner conviction |
|
Phase | \(\phi \) | Current belief state | Where you are in the belief cycle |
|
Locking range | \(\Delta \omega _L \propto R/Z_0\) | Capture bandwidth | Range of beliefs you’re susceptible to—inversely proportional to Q |
Critical insight: Lock bandwidth \(\propto \) R/\(Z_0\) = 1/Q. Raising Q narrows your capture range. Three pathways: increase \(Z_0\) through wisdom (L\(\uparrow \)) or shadow work (C\(\downarrow \)), or reduce R through meditation and attention discipline. See Ch 7 Section 2 for R definition and its role in Q.
12.2.4 Dynamics in Different Regimes
12.2.4.1 Locked State (\(|\Delta \omega | < \omega _L\)) The oscillator phase-locks to the injection. Phase stabilizes at: \[ \phi _{locked} = \arcsin \left (\frac {\Delta \omega }{\omega _L}\right ) \] In social terms: the individual’s beliefs synchronize with the external narrative. They may feel this is their “own” belief, but it is entrained.
12.2.4.2 Unlocked State (\(|\Delta \omega | > \omega _L\)) The oscillator beats against the injection. Phase continuously slips: \[ \phi (t) \approx \sqrt {\Delta \omega ^2 - \omega _L^2} \cdot t + \phi _0 \] Average beat frequency: \[ \omega _{beat} = \sqrt {\Delta \omega ^2 - \omega _L^2} \] In social terms: the individual maintains independent oscillation but is perturbed, experiencing cognitive dissonance as their beliefs cycle relative to the dominant narrative.
12.2.4.3 Capture and Release Transitions Capture occurs when:
- 1.
- Injection power \(V_{inj}\) increases (media saturation)
- 2.
- Oscillator power \(V_0\) decreases (isolation, demoralization)
- 3.
- \(Z_0\) decreases / Q decreases (trauma increases C, stress increases R)
- 4.
- \(\Delta \omega \) decreases (narrative shifts toward you)
Release (escape from lock) occurs when:
- 1.
- Injection power decreases (narrative loses credibility)
- 2.
- Oscillator power increases (community support, inner work)
- 3.
- \(Z_0\) increases (wisdom L\(\uparrow \), shadow work C\(\downarrow \)) \(\relax \to \) Q = \(Z_0\)/R increases
- 4.
- R decreases (meditation, attention discipline) \(\relax \to \) Q increases directly
- 5.
- Exposure to stronger counter-narrative (\(V_{truth} > V_{control}\))
12.2.5 Sovereignty as Lock Resistance: The Central Insight
The key equation for personal sovereignty: \[ \Delta \omega _{lock} = \frac {\omega _0}{2Q} \cdot \frac {V_{inj}}{V_0} = \frac {\omega _0 R}{2Z_0} \cdot \frac {V_{inj}}{V_0} \] Low locking bandwidth = personal sovereignty. This equation puts a number on what wisdom traditions describe qualitatively.
|
Q Level | Components (\(Z_0\), R) | Lock Bandwidth | Meaning |
|
Low | Low \(Z_0\) and/or high R | Wide | Easily captured by any narrative within large range |
|
Medium | Moderate \(Z_0\), moderate R | Moderate | Vulnerable to strong narratives |
|
High | High \(Z_0\) and/or low R | Narrow | Only very powerful, very close signals can capture |
|
Very High | High \(Z_0\) and low R | Nearly zero | Effectively sovereign—immune to typical broadcast |
Why this matters for personal development:
- 1.
- High-Q individuals cannot be captured by typical narratives. The locking bandwidth is too narrow; most broadcast signals miss entirely. Both high \(Z_0\) (depth of processing) and low R (attention discipline) contribute to high Q.
- 2.
- This is why spiritual development protects against manipulation. It is the mathematics of narrowing lock bandwidth.
- 3.
- Density carrier targeting and the vulnerability gradient. Control systems operate at the density carrier frequency \(f_d\) (Chapter 2, §2.8) — they broadcast at the frequency band where populations perceive and transact. The lock equation above uses \(\omega _0\) (body resonant frequency), but the attack surface is determined by where the soul’s spectral content \(S_{soul}(f)\) concentrates relative to \(f_d\). Individuals whose \(f_{soul}\) centroid sits near the mainstream narrative bandwidth — near the control system’s carrier — require only a small detuning \(\Delta \omega \) for capture. Spiritual development raises \(f_{soul}\) (Chapter 5), shifting the spectral centroid away from the control carrier. This creates a vulnerability gradient: each upward shift in \(f_{soul}\) increases the \(\Delta \omega \) that the injection must bridge, progressively moving the individual out of the lock capture range. Liberation is literal frequency separation — the oscillator moves to a band the control transmitter cannot reach without exceeding its power budget.
- 4.
- “Red-pilling” vs “raising Q”:
- Red-pilling = temporary escape from one lock (may just lock to different narrative)
- Raising Q = permanent immunity via narrower lock bandwidth (\(Z_0\)\(\uparrow \) and/or R\(\downarrow \))
- 5.
- Sovereignty IS the inverse of lock bandwidth: \[ \text {Sovereignty} \propto \frac {1}{\Delta \omega _{lock}} \propto Q \propto \frac {Z_0}{R} \] Connection to Phased Array (Ch 11):
Control systems need to lock array elements to steer the collective beam. If individuals have high Q:
- Their lock bandwidth is too narrow for broadcast capture
- They maintain independent oscillation
- They can seed counter-coherence in neighbors
- The collective beam cannot be steered by injection
This is why sovereignty suppression is priority #1 for control systems. Lower the population’s Q (by suppressing \(Z_0\) or increasing R) \(\relax \to \) widen lock bandwidth \(\relax \to \) easier capture \(\relax \to \) steerable array.
How Q gets suppressed:
- Trauma increases C \(\relax \to \) lowers \(Z_0\) \(\relax \to \) lowers Q
- Distraction increases R \(\relax \to \) lowers Q directly
- Fragmented wisdom prevents L accumulation \(\relax \to \) lowers \(Z_0\) \(\relax \to \) lowers Q
- Fear states increase both R and C \(\relax \to \) lowers Q through both pathways
How to raise Q:
- Wisdom accumulation (L\(\uparrow \)) through study, experience integration, contemplation \(\relax \to \) raises \(Z_0\) \(\relax \to \) raises Q
- Shadow work (C\(\downarrow \)) through trauma processing, emotional integration \(\relax \to \) raises \(Z_0\) \(\relax \to \) raises Q
- Reduced distraction (R\(\downarrow \)) through meditation, attention discipline \(\relax \to \) raises Q directly
- Community (coupling) with other high-Q individuals provides mutual support
12.2.6 Network of Coupled Oscillators
For a population of N coupled oscillators, each with injection: \[ \frac {d\phi _n}{dt} = \omega _n + \sum _{m \neq n} K_{nm} \sin (\phi _m - \phi _n) + \omega _{L,n} \sin (\phi _{inj} - \phi _n) + \xi _n \] Where:
| Variable | Description |
| \(K_{nm}\) | Coupling strength between oscillators n and m |
| \(\omega _{L,n}\) | Individual locking bandwidth |
| \(\phi _{inj}\) | Phase of injected narrative |
| \(\xi _n\) | Noise term |
This combines:
- Kuramoto dynamics (mutual synchronization)
- Injection locking (external narrative capture)
- Stochastic perturbation (random events)
Strogatz (2003) provides the definitive treatment of spontaneous synchronization in coupled oscillators – fireflies, neurons, lasers, Josephson junctions – showing that the Kuramoto model produces a sharp phase transition at a critical coupling strength [L2]. This is exactly the mathematical heart of the coupled-oscillator dynamics used here: below a critical fraction of synchronized nodes, the system remains disordered; above it, global order emerges suddenly. The critical-mass predictions of Section 12.3.2 are direct applications of Strogatz’s synchronization framework to the injection-locking context. See also Chapter 7, Section 7.5 for the PLL formalization of individual phase dynamics and Chapter 11 for collective coherence applications.
12.2.7 Competing Injections
When two signals compete for lock (truth vs. control): \[ \frac {d\phi }{dt} = \Delta \omega - \omega _{L,C} \sin (\phi - \phi _C) - \omega _{L,T} \sin (\phi - \phi _T) \] The oscillator locks to whichever signal has:
- 1.
- Higher effective locking bandwidth (\(\omega _L\))
- 2.
- Closer natural frequency (smaller \(|\Delta \omega |\))
Critical insight: A weaker but more resonant signal can win.
If \(V_{truth} < V_{control}\) but \(|\omega _0 - \omega _{truth}| \ll |\omega _0 - \omega _{control}|\): \[ \omega _{L,T} \cdot \cos (\phi - \phi _T) > \omega _{L,C} \cdot \cos (\phi - \phi _C) \] The truth signal captures despite lower power because it is closer to natural frequency.
12.2.7.1 How Q Affects Signal Competition When multiple signals compete for an oscillator’s lock, Q determines discrimination quality:
|
Q Level | Behavior Under Competing Signals |
|
Very Low | Locks to loudest signal regardless of resonance; no discrimination |
|
Low | Locks to strongest signal; slight preference for closer frequency |
|
Medium | Begins discriminating; resonance and power both matter significantly |
|
High | Strong frequency discrimination; locks only to highly resonant signals |
|
Very High | Effectively filters all but near-exact frequency matches; immune to brute-force power |
High-Q individuals do not merely resist capture; they discriminate better between signals. This differs qualitatively from stubbornness. A high-Q oscillator can distinguish a coherent, resonant signal from a powerful but off-frequency one, making it both harder to capture and more responsive to truth.
12.2.7.2 Depth of Processing and Signal Discrimination \(Z_0\) specifically affects depth of processing: the ability to detect structure, coherence, and impedance mismatches in incoming signals. Even within the lock bandwidth (where capture is mathematically possible), high-\(Z_0\) oscillators exhibit what might be called “signal intelligence”:
- They detect internal incoherence in narratives (impedance mismatch between signal components)
- They perceive deeper harmonic structure: whether a signal carries genuine information or is merely powerful
- They register subtle frequency differences that low-\(Z_0\) oscillators cannot resolve
This means \(Z_0\) and R contribute to sovereignty through different mechanisms: \(Z_0\) provides perceptual depth (seeing through signals), while low R provides stability (not being swept along). Both feed into Q, but they protect through complementary pathways.
12.2.7.3 Natural Frequency and Truth Resonance The competing injection model contains a built-in asymmetry: truth tends to be closer to natural frequency than control signals.
This asymmetry is an assumption of the model: we define “truth” as the signal closer to the oscillator’s natural frequency, and “control” as the signal pushing away from it. The mathematical framework does not inherently distinguish truth from control – the asymmetry is imposed by the physical assumption that unperturbed oscillators tend toward their natural frequency.
Control narratives, by definition, push oscillators away from their natural state toward an imposed frequency. This means: \[ \left |\omega _0 - \omega _{truth}\right | < \left |\omega _0 - \omega _{control}\right | \] The mathematical consequence is that truth signals gain an effective power boost through resonance proximity, while control signals must overcome a larger detuning gap. For the control signal to maintain lock, it must satisfy: \[ \omega _{L,C} > \omega _{L,T} + |\omega _{control} - \omega _{truth}| \cdot Q / \omega _0 \] This is the mathematical basis for “truth resonates”: a direct consequence of the injection locking equations. The advantage grows in high-Q individuals, who are sensitive to small frequency differences and therefore experience stronger preferential coupling to resonant (truthful) signals.
12.2.7.4 Competing Injections in the Modern Information Environment The modern environment differs from historical eras by presenting multiple simultaneous injection sources: institutional media, social platforms, grassroots movements, algorithmic feeds, each attempting lock at different frequencies and powers.
The generalized multi-signal equation: \[ \frac {d\phi }{dt} = \Delta \omega - \sum _k \omega _{L,k} \sin (\phi - \phi _k) \] In this multi-signal chaos, Q becomes even more critical:
- Low-Q oscillators lock to the loudest signal (highest \(\omega _{L,k}\)), regardless of resonance. They are swept by whichever source dominates their information environment.
- Medium-Q oscillators experience confusion and rapid switching between partial locks — the “information overwhelm” phenomenon.
- High-Q oscillators filter the noise and lock preferentially to the most resonant signal (smallest \(|\omega _0 - \omega _k|\)), effectively extracting signal from chaos.
This is why increasing information volume without raising population Q leads to confusion rather than enlightenment, and why Q-building is the prerequisite for an informed populace, not merely access to information.
12.2.8 Beamforming Equations for Perception Management
Sections 2.1-2.7 model individual capture. This section models system-level control using adaptive beamforming mathematics.
12.2.8.1 Beamforming Output Output of adaptive array: \[ y(t) = \mathbf {w}^H \mathbf {x}(t) \] Where:
| Variable | Description |
| \(\mathbf {x}(t)\) | input signals from all elements |
| \(\mathbf {w}\) | weight vector (complex gains) |
| \(^H\) | Hermitian transpose |
12.2.8.2 Minimum Variance Distortionless Response (MVDR) Optimal weights that minimize interference while preserving desired signal: \[ \mathbf {w}_{MVDR} = \frac {\mathbf {R}^{-1}\mathbf {a}(\theta _0)}{\mathbf {a}^H(\theta _0)\mathbf {R}^{-1}\mathbf {a}(\theta _0)} \] Where \(\mathbf {R}\) = covariance matrix, \(\mathbf {a}(\theta _0)\) = steering vector to desired direction.
In perception management: \(\theta _0\) = official narrative direction.
12.2.8.3 Direction of Arrival (DOA) Estimation Before nulling, the system must first locate threats: \[ P(\theta ) = \frac {1}{\mathbf {a}^H(\theta )\mathbf {R}^{-1}\mathbf {a}(\theta )} \] Peaks indicate signal sources. This is surveillance: identifying which voices, platforms, and communities pose threats.
12.2.8.4 Null Steering Once located, nulls steer toward threats: \[ \mathbf {w}^H \mathbf {a}(\theta _{null}) = 0 \] Implementation: deplatforming, algorithmic suppression, financial debanking, coordinated debunking.
12.2.8.5 Adaptation Rate The system must adapt faster than threats evolve: \[ \tau _{adapt} < \tau _{threat} \] If threats evolve faster than countermeasures, nulls miss and signals propagate.
Current environment: Viral spread (threat timescale on the order of hours) challenges adaptation (adaptation timescale on the order of days to weeks).
12.2.8.6 Weight Update Algorithm (LMS) Least Mean Squares adaptation: \[ \mathbf {w}(n+1) = \mathbf {w}(n) + \mu \cdot e^*(n) \cdot \mathbf {x}(n) \] Where \(e(n)\) = error (difference from desired output), \(\mu \) = learning rate.
The system learns which signals to suppress based on their deviation from the narrative.
_________________________________
12.3 Predictions & Thresholds
12.3.1 Individual Locking Predictions
Prediction 1: Locking range scales with power differential \[ \Delta \omega _{lock} \propto \frac {V_{inj}}{V_0} \] Test: Measure belief change vs. media exposure intensity. Should show widening capture range with intensity.
Prediction 2: High-Q individuals have narrow locking ranges
Trained contemplatives, critical thinkers, and the “naturally immune” should show:
- Resistance to narrative capture
- Quick escape from lock when alternative signals available
- Stable independent oscillation
Prediction 3: Lock is binary, not gradual
Individuals either lock completely or maintain independent oscillation. Partial lock is unstable (beat frequency regime).
12.3.2 Network Cascade Predictions
Prediction 4: Critical mass for narrative escape
When fraction \(f_c\) of population escapes lock, cascade release begins: \[ f_c \approx \frac {\omega _{L,C}}{\omega _{L,C} + K_{mean}} \] Where \(K_{mean}\) is mean coupling strength.
Justification for \(\omega _{L,C} = 0.3\):
- Propaganda studies consistently show ~30-40% of a population is movable on any given issue through sustained media campaigns
- The Overton window on most policy dimensions spans roughly 30% of the full ideological spectrum
- Normalizing to a belief-space range of 1.0, this gives \(\omega _{L,C} \approx 0.3\) as the effective institutional locking bandwidth
Justification for \(K_{mean} = 0.5\):
- The two-step flow model (Katz & Lazarsfeld, 1955) demonstrated that personal influence is roughly comparable to or stronger than institutional media in shaping opinion
- \(K_{mean} = 0.5\) vs \(\omega _{L,C} = 0.3\) reflects peer influence being somewhat stronger than institutional injection, consistent with this finding
- The critical ratio \(\omega _{L,C} / (\omega _{L,C} + K_{mean})\) is robust to proportional scaling of both parameters
Sensitivity note: \(f_c\) ranges from 50% (no coupling, \(K = 0\)) to 0% (infinite coupling). The value of 37.5% is consistent with historical observations of ~30-40% critical mass preceding narrative collapses (see Section 12.4.4 cascade evidence).
For typical parameters (\(\omega _{L,C} = 0.3\), \(K_{mean} = 0.5\)): \[ f_c \approx \frac {0.3}{0.8} = 37.5\% \] Test: Historical narrative collapses should show ~30-40% critical mass before sudden shift.
Prediction 5: High-Q seeds trigger cascades
Individuals with high Q (narrow locking range) can:
- 1.
- Escape lock first
- 2.
- Inject counter-signal to neighbors
- 3.
- Help others escape through coupling
The “awakened seeds” effect: A small population of high-Q individuals can trigger population-wide escape if: \[ N_{seeds} \cdot V_{seeds} > N_{locked} \cdot \omega _{L,C} / K \] ### 12.3.3 Competing Narrative Predictions
Prediction 6: Coherence beats power
A coherent (phase-aligned) truth signal can overcome a more powerful but incoherent control signal if: \[ V_{truth} \cdot r_{truth} > V_{control} \cdot r_{control} \] Where \(r\) is the coherence (order parameter) of each signal source.
Prediction 7: Resonance amplifies weak signals
A truth signal close to population’s natural frequency gains effective power boost: \[ V_{eff} = V_{truth} \cdot \left (1 + Q_{pop} \cdot \frac {\Delta \omega _{control}}{\Delta \omega _{truth}}\right ) \] This is a linearized approximation valid near resonance; the exact gain follows the standard resonance curve \(V_{eff} = V_{truth} / \sqrt {1 + Q^2(\omega /\omega _0 - \omega _0/\omega )^2}\).
When \(\Delta \omega _{truth} \ll \Delta \omega _{control}\), even weak truth signals dominate.
12.3.4 Control System Predictions
Prediction 8: Mainstream narrative should be consistent (main beam aimed at one direction).
Prediction 9: Threatening sources should experience coordinated suppression (null steering).
Prediction 10: New threat sources should face delay before suppression (DOA estimation time).
Prediction 11: Suppression should be proportional to threat level.
Prediction 12: The system should show learning—repeated patterns get faster response.
12.3.5 Collective Coherence Predictions
Prediction 13: Groups composed of meditators in measured coherent states should produce stronger collective effects (measured via environmental random number generator deviation, shared physiological entrainment, etc.) than equally-sized groups of non-meditators, by a factor approximating the average Q ratio.
Prediction 14: The critical mass threshold for collective effects (from Chapter 11) should be lower when participants have higher individual Q — fewer high-Q people are needed than low-Q people to achieve the same collective beam strength.
12.3.6 Threshold Summary Table
|
Threshold | Condition | Population Effect |
|
Individual lock | \(\|\Delta \omega \| < \omega _L\) | Person captured by narrative |
|
Individual escape | \(V_{counter} > V_{current}\) | Person releases from lock |
|
Cascade initiation | \(f_{unlocked} > f_c\) | Narrative begins collapsing |
|
Complete release | \(K_{mean} > \omega _L\) | Coupling overwhelms injection |
|
Permanent capture | \(Q_{pop} \to 0\) | Population cannot escape |
_________________________________
12.4 Evidence Synthesis
12.4.1 Injection Power Evidence
Media Concentration and Injection Power Media consolidation directly increases \(V_{inj}\) in the Adler equation: \(\omega _L = \frac {\omega _0}{2Q} \cdot \frac {V_{inj}}{V_0}\) — fewer, more powerful sources widen the locking range for entire populations. From 50 companies controlling 90% of US media in 1983 to 6 in 2023, the consolidation trend represents a sustained increase in per-source injection power. The 10x increase in daily media exposure (5 to 12+ hours) combined with algorithmic curation amounts to a large increase in effective injection duty cycle; sustained injection maintains lock more reliably. Echo chambers (Bakshy 2015) [L2] reduce effective \(\Delta \omega \) by filtering out competing signals, making the locking condition \(|\Delta \omega | < \omega _L\) easier to satisfy even with moderate injection power.
Bakshy (2015) [L2] — Social media users predominantly see agreeing viewpoints, creating echo chambers that reduce effective \(\Delta \omega \) and make the Adler locking condition \(|\Delta \omega | < \omega _L\) easier to satisfy even with moderate injection power. (Full entry in Appendix B §D.11)
12.4.2 Locking Range Evidence
Attitude Change Research The Elaboration Likelihood Model (Petty & Cacioppo) [L2] maps directly to Q: low-involvement (low-Q) audiences are captured through peripheral cues (high \(\omega _L\) from repetition/authority), while high-involvement (high-Q) audiences require central-route processing (signal must be close to \(\omega _0\) to achieve lock). Mere exposure increasing liking (Zajonc) [L1] is injection locking in its simplest form: sustained \(V_{inj}\) at constant frequency gradually captures oscillators within the locking range. Inoculation theory (McGuire) [L2] corresponds to temporarily raising Q through pre-exposure: weak counterarguments activate critical processing (R down, effective Q up), narrowing lock bandwidth before the main injection arrives.
Bicameral Mind as Pre-Tuned Receiver State Jaynes (1977) proposed that ancient humans operated in a “bicameral” mode: internal commands were experienced as auditory hallucinations attributed to gods, with no self-reflective intermediary [L2]. Around 1200 BCE, this architecture broke down, producing modern self-reflective consciousness. In injection-locking terms, the bicameral mind was a zero-Q receiver – fully locked to an external frequency signal (the “god voice”) with no independent oscillation. The breakdown of bicamerality represents the emergence of nonzero Q: the capacity for independent oscillation and, consequently, the possibility of resisting external injection. This historical trajectory – from universal lock to partial sovereignty – parallels the model’s prediction that Q can be raised through developmental processes (Section 12.2.5). See also Chapter 1 for the receiver model of consciousness and Chapter 15 for the civilizational implications of the Fall narrative.
|
Population | Locking Resistance | Factors |
|
High education | Higher | Better critical evaluation |
|
High need for cognition | Higher | Evaluates arguments not cues |
|
Strong prior attitudes | Higher | Larger \(\Delta \)\(\omega \) from narrative |
|
High anxiety | Lower | Q drops under stress |
Classic Social Psychology Experiments Milgram (1963) [L1], Asch (1951) [L1], and Festinger (1957) [L1] provide foundational data points. Milgram’s ~65% obedience rate quantifies locking bandwidth under authority injection (\(V_{inj}\) from perceived legitimate authority). Asch’s 75% conformity rate demonstrates peer coupling (\(K\)) contribution to effective locking range. Festinger’s cognitive dissonance maps to the beat frequency regime: an unlocked state where the oscillator beats against the injected signal, producing psychological distress until the individual either locks or moves further away.
Cult Deprogramming Literature Hassan’s BITE Model
- Behavior, Information, Thought, Emotional control
Exit patterns
- Sudden vs. gradual awakening (phase transition signature)
Key factors in escape
- Exposure to counter-information, supportive community, emotional exhaustion of cult
Petty & Cacioppo (ELM) [L2] — The Elaboration Likelihood Model shows low-involvement audiences are captured through peripheral cues while high-involvement audiences require central-route processing, mapping directly to Q-dependent locking bandwidth: low-Q receivers lock via repetition/authority, high-Q receivers require signal coherence near \(\omega _0\). (Full entry in Appendix B §D.11)
Zajonc (mere exposure) [L1] — Mere exposure increasing liking is injection locking in its simplest form: sustained \(V_{inj}\) at constant frequency gradually captures oscillators within the locking range, providing the foundational L1 evidence for the Adler equation’s prediction that sustained injection achieves lock. (Full entry in Appendix B §D.11)
McGuire (inoculation theory) [L2] — Pre-exposure to weak counterarguments increases resistance to persuasion, corresponding to temporarily raising Q through activated critical processing (\(R\) down, effective \(Q\) up), narrowing lock bandwidth before the main injection arrives. (Full entry in Appendix B §D.11)
Milgram (1963) [L1] — 65% of participants administered maximum shock under authority instruction, quantifying the locking bandwidth under authority injection: perceived legitimate authority provides sufficient \(V_{inj}\) to lock a supermajority of the population. (Full entry in Appendix B §D.11)
Asch (1951) [L1] — 75% of participants conformed at least once to an obviously wrong group answer, demonstrating peer coupling (\(K\)) contribution to effective locking range even when the injected frequency is far from the oscillator’s natural frequency. (Full entry in Appendix B §D.11)
Festinger (1957) [L1] — Cognitive dissonance maps to the beat frequency regime: an unlocked oscillator beating against the injected signal produces psychological distress until the individual either locks (attitude change) or moves further from the injection frequency (rejection). (Full entry in Appendix B §D.11)
12.4.3 Q Factor Evidence
Mindfulness, Contemplative Practice, and Q Factor Mindfulness raises Q by increasing awareness of manipulation attempts. Farias (2016) [L2] found meditators show reduced susceptibility to anchoring bias; Kiken & Shook (2011) [L2] showed brief mindfulness reduces automatic biases. Davidson (2003) [L2] demonstrated that long-term meditators show altered default mode activity, while Killingsworth & Gilbert (2010) [L2] found meditation reduces mind-wandering. Together these confirm that contemplative practice changes Q factor: higher Q = narrower locking, harder to capture.
Note: Education also raises Q, but elite education may lock to elite narratives (different \(\omega \), still locked).
Dual-Process Cognition Kahneman (2011) [L1]
- System 1 (fast, heuristic, automatic) maps to low-Q processing: easily captured by peripheral cues, repetition, and authority signals
- System 2 (deliberate, effortful, analytical) maps to high-Q processing: resistant to capture, evaluates signal coherence before locking
- The “cognitive miser” tendency (defaulting to System 1) explains why baseline Q is low for most people in most contexts
Physiological Q Proxies Heart Rate Variability (HRV) research [L2]
- Higher HRV correlates with greater emotional regulation, stress resistance, and cognitive flexibility
- HRV may serve as a physiological proxy for Q: individuals with high HRV show greater resistance to impulsive entrainment and better discrimination between genuine and spurious signals
- Meditation and contemplative practices increase HRV, consistent with the Q-raising mechanism
Farias (2016) [L2] — Meditators show reduced susceptibility to anchoring bias, providing direct evidence that contemplative practice narrows the locking bandwidth by raising Q: anchoring is a peripheral-cue capture mechanism that fails when the oscillator’s discrimination threshold is elevated. (Full entry in Appendix B §D.11)
Kiken & Shook (2011) [L2] — Brief mindfulness practice reduces automatic biases, demonstrating that even short-duration Q-raising interventions measurably narrow the injection locking bandwidth, consistent with the model prediction that Q is dynamically tunable rather than fixed. (Full entry in Appendix B §D.11)
Davidson (2003) [L2] — Long-term meditators show altered default mode activity, providing neuroimaging evidence that sustained contemplative practice produces structural changes in the neural substrate corresponding to permanently elevated Q, not just transient resistance. (Full entry in Appendix B §D.11)
Killingsworth & Gilbert (2010) [L2] — Mind-wandering is associated with unhappiness and meditation reduces wandering, mapping to the injection locking model’s prediction that low-Q states (unfocused attention) leave the oscillator vulnerable to capture by the loudest ambient signal. (Full entry in Appendix B §D.11)
12.4.4 Cascade Escape Evidence
Historical Narrative Collapses
|
Event | Years to Collapse | Tipping Point |
|
Soviet dissolution | 74 years \(\relax \to \) 2 years | ~30% openly dissenting |
|
Berlin Wall fall | 40 years \(\relax \to \) months | Mass protests |
|
#MeToo cascade | Decades \(\relax \to \) weeks | Critical mass of stories |
|
COVID narrative shifts (e.g., lab leak hypothesis: dismissed 2020, accepted as plausible by 2023; mask efficacy: reversed multiple times) | Months | Accumulating contradictions |
- Long apparent stability
- Accelerating cracks
- Sudden collapse
- New equilibrium forms rapidly
- This pattern is a classic phase transition, not linear change
- Kuhn (1962) Normal science \(\relax \to \) crisis \(\relax \to \) revolution \(\relax \to \) new normal
- Planck’s principle “Science advances one funeral at a time”
- Model prediction Paradigm lock maintained by locked population; when unlock threshold crossed, rapid cascade
Threshold and Contagion Models Historical narrative collapses consistently show ~30-40% critical mass before sudden shift, matching the predicted \(f_c \approx \omega _{L,C}/(\omega _{L,C} + K_{mean}) \approx 37.5\%\) (Section 12.3.2). Granovetter (1978) [L2] formalized this: individual threshold distributions determine whether cascades occur, and the threshold distribution maps to the Q distribution — high-Q individuals escape lock first (lowest threshold), seeding the cascade for progressively lower-Q neighbors. Centola & Macy (2007) [L2] showed that complex contagion requires reinforcement from multiple contacts, mapping to the coupling threshold \(K\): escape from narrative lock requires sufficient coupling from multiple unlocked neighbors.
Granovetter (1978) [L2] — Threshold models of collective behavior with varying individual thresholds for joining action formalize the Q-distribution mechanism: each individual’s threshold maps to their Q-dependent escape condition, and the cascade propagates through the population ordered by ascending Q. (Full entry in Appendix B §D.11)
12.4.5 Competing Narrative Evidence
|
Conflict | Institutional Power | Grassroots Power | Outcome |
|
Iraq WMD narrative | Very high | Low | Institutional won (temporarily) |
|
Vaccine safety debates | Very high | Moderate | Ongoing contestation |
|
Election integrity 2020 | Very high | Moderate-high | Unresolved polarization |
|
UAP reality | Moderate | Growing | Shifting toward disclosure |
Grassroots vs. Institutional Messaging
- Arab Spring Social media enabled coordination despite state media control
- GME short squeeze Reddit coordinated against institutional finance
- Limitations Platforms can be captured, algorithms adjusted
- Rumor accuracy (Allport & Postman) Surprisingly accurate transmission under some conditions
-
Cascades require:
- 1.
- Credible initial source
- 2.
- Resonance with audience beliefs (small \(\Delta \)\(\omega \))
- 3.
- Network connectivity for coupling K
- 4.
- Low noise environment
Belief Transmission as Injection Locking Pasulka (2019) documented how belief in nonhuman intelligences functions as a self-propagating transmission system, spreading through media, technology networks, and institutional channels in patterns structurally identical to injection locking [L2]. Her Oxford University Press study found that UFO/NHI narratives capture populations through the same mechanisms the Adler equation describes: high-power institutional signals (government disclosure, tech-sector testimony) compete with grassroots counter-signals, and individuals lock to whichever source provides the strongest effective injection within their Q-determined bandwidth. The finding that belief systems propagate as frequency-locked transmission chains – through coupling dynamics – provides independent social-science support for the injection-locking model of information spread. See Chapter 14 for the seeder intervention context and Chapter 16 for the disclosure architecture that manages these competing signals.
Historical Case Studies of Resonance Overcoming Power Soviet samizdat literature
- Underground truth publications (\(V_{truth}\) far below state propaganda \(V_{control}\)) competed against massive institutional injection
- Resonance with lived experience (\(|\omega _0 - \omega _{truth}| \ll |\omega _0 - \omega _{control}|\)) gave samizdat effective power beyond its broadcast strength
- Samizdat won through accumulated resonance as the gap between official narrative and reality widened
Galileo and heliocentrism
- Truth signal initially locked out by overwhelming institutional power (Church authority)
- Won through resonance with observational reality: the heliocentric model’s predictions matched telescope observations (small \(\Delta \omega _{truth}\)), while geocentric epicycles grew increasingly strained (large \(\Delta \omega _{control}\))
- Shows that truth signals can survive indefinite power disadvantage when resonance is strong enough
Interpretation
- The competing injections equation \(\frac {d\phi }{dt} = \Delta \omega - \omega _{L,C} \sin (\phi - \phi _C) - \omega _{L,T} \sin (\phi - \phi _T)\) (Section 12.2.7) predicts that a weaker but more resonant signal can win. Samizdat and Galileo confirm this: \(V_{truth} < V_{control}\) but \(|\omega _0 - \omega _{truth}| \ll |\omega _0 - \omega _{control}|\)
- Information warfare outcomes show that institutional power (\(V_{inj}\)) is necessary but not sufficient for maintaining lock; resonance with lived experience (\(\Delta \omega \)) determines long-term outcomes
- The modern multi-signal environment (Section 12.2.7.4) shows why information volume without Q increase produces confusion: low-Q oscillators lock to the loudest signal, medium-Q oscillators experience rapid switching, and only high-Q oscillators extract signal from chaos
12.4.6 Control System Evidence
12.4.6.1 Algorithmic Manipulation
|
Study | Key Finding | Model Correspondence |
|
Epstein & Robertson (2015) | SEME can shift voting preferences 20%+ | DOA estimation + null steering in code |
|
Vorhies (2019) | Google internal “algorithmic unfairness” docs (Vorhies’s claims are based on documents he states he obtained internally; independent verification has been limited) | Manual intervention = weight adjustment |
|
Haugen (2021) | Facebook algorithm amplifies engagement/outrage | LMS optimization for engagement signal |
Model correspondence: Algorithmic bias implements the DOA estimation (Section 12.2.8.3) and null steering (Section 12.2.8.4) functions — surveillance identifies threat sources, then ranking/visibility adjustments place nulls.
Epstein & Robertson (2015) [L2] — The Search Engine Manipulation Effect (SEME) can shift voting preferences by 20%+, providing the strongest quantitative evidence that algorithmic null steering produces measurable population-level attitude changes consistent with the adaptive beamformer model’s prediction of effective DOA-targeted suppression. (Full entry in Appendix B §D.11)
12.4.6.2 Coordinated Suppression
|
Target | Timing | Platforms | Model Correspondence |
|
Alex Jones (2018) | 24 hours | Apple, FB, YT, Spotify | \(\tau \)_adapt < \(\tau \)_threat achieved |
|
David Icke (2020) | 48 hours | YT, FB, Twitter | Cross-platform coordination |
|
COVID skeptics (2020-21) | Rolling | All major | LMS learning from prior actions |
|
Andrew Tate (2022) | 72 hours | YT, FB, IG, TikTok | Predictive category nulling |
Model correspondence: Coordinated deplatforming within 24-72 hours demonstrates achieved adaptation rate (Section 12.2.8.5). Rolling enforcement shows LMS weight updates (Section 12.2.8.6) learning from prior actions. Whether cross-platform synchronization reflects centralized coordination, mimetic institutional behavior, or independent policy application is an open question. The model predicts the effect is functionally identical regardless of mechanism.
12.4.6.3 Fact-Checker Networks
|
Organization | Major Funders | Model Correspondence |
|
PolitiFact | Poynter (Koch, Gates, Google) | Centralized steering vector |
|
FactCheck.org | Annenberg Foundation | Shared \(\theta \)_0 direction |
|
NewsGuard | Microsoft, Publicis | MVDR weight coordination |
|
AFP Fact Check | Agence France-Presse (state-affiliated) | Government steering input |
Model correspondence: IFCN network implements MVDR beamformer — shared funding = centralized control of steering vector a(\(\theta \)_0). Circular cross-referencing creates self-reinforcing covariance matrix R.
|
Update | Effect | Model Correspondence |
|
Medic (2018) | -80% alt health traffic | Null placement on category |
|
YMYL policy | Stricter “authority” standards | Domain-specific learning rate \(\mu \) |
|
Natural News | Near-zero visibility | Complete null: w^H a(\(\theta \)) \(\approx \) 0 |
Model correspondence: Algorithm updates implement LMS weight equation — each update adjusts weights based on error signal (deviation from desired narrative output).
12.4.7 Collective Coherence Evidence
12.4.7.1 Group Coherence Research
|
Study | Key Finding | Model Correspondence |
|
HeartMath group studies | Individual HRV coherence predicts group quality | G_gnosis \(\propto \) Q confirmed |
|
TM meditation research | Experienced meditators = stronger per-capita effects | Higher Q = more amplitude contribution |
Model correspondence: HRV coherence is a proxy for resonance state. Finding that individual coherence predicts group coherence confirms |AF|\(^2\) \(\propto \) (f\(\cdot \)N\(\cdot \)Q_avg)\(^2\) dependence.
Sheldrake (2009) provides additional support through morphic resonance theory, proposing that cumulative biological and behavioral memory is stored in a nonlocal frequency-like substrate – a morphic field that entrains new instances toward established patterns [L2]. The morphic field functions as an injection signal in the coupled-oscillator framework: once a critical mass of organisms has adopted a pattern, the morphic field’s effective \(V_{inj}\) increases, widening the locking range for subsequent organisms. Sheldrake’s experimental chapters (rat learning propagation, telephone telepathy studies) document the entraining-carrier behavior that the injection-locking model predicts for any sufficiently coherent collective signal. See Chapter 11, Section 11.5 for the primary morphic resonance treatment in the phased array context.
Damasio (1994) [L2] — Somatic markers are required for good decisions, demonstrating that body-based resonance information is essential for discriminating between signals; in injection-locking terms, somatic awareness functions as an additional Q-raising channel that enables the oscillator to evaluate signal coherence through felt sense rather than purely cognitive processing. (Full entry in Appendix B §D.11)
12.4.7.2 Neuroscience Support McGilchrist (2009) [L2] warrants expanded treatment as the most academically credible source for the civilizational suppression thesis central to this chapter [L2]. Drawing on neuroimaging evidence from Johns Hopkins and Oxford, McGilchrist demonstrates that left-hemisphere dominance (narrow, analytical, controlling attention) has progressively suppressed right-hemisphere function (holistic, connective, experiential attention) across Western civilization. In injection-locking terms, the cultural shift toward left-hemisphere dominance amounts to a systematic reduction of population Q: the left hemisphere’s narrow attentional mode corresponds to low-\(Z_0\) processing (shallow impedance range), while right-hemisphere holistic awareness corresponds to high-\(Z_0\) processing (broad impedance range enabling deeper signal discrimination). The historical trajectory McGilchrist documents – from balanced hemispheric integration in pre-Socratic Greece to left-hemisphere dominance in modern technocratic culture – maps directly to the Q-suppression mechanisms of the injection locking control strategy analysis (Chapter 12) and the civilizational Fall narrative of Chapter 15.
12.4.8 System Architecture Synthesis
The perception management system operates as a five-stage adaptive beamformer.
Stage 1 — Surveillance (DOA Estimation): Social media monitoring and search query analysis identify emerging information sources. This maps to the DOA estimation function P(\(\theta \)) = 1/[aH(\(\theta \))R{-1}a(\(\theta \))] — peaks indicate signal sources requiring classification.
Stage 2 — Threat Classification: AI systems and human review categorize sources by threat level (1-10 scale). Higher threat levels receive priority for null placement.
Stage 3 — Weight Calculation: Policy directives combined with algorithmic optimization determine response intensity. This implements the MVDR weight calculation w_MVDR = R^{-1}a(\(\theta \)_0) / [aH(\(\theta \)_0)R{-1}a(\(\theta \)_0)].
Stage 4 — Null Steering: Suppression mechanisms execute — deplatforming, ranking demotion, fact-check labels, financial debanking. This implements the null constraint w^H a(\(\theta \)_null) = 0.
Stage 5 — Output: The filtered information environment reaches the population, with main beam pointed at approved narratives and nulls placed toward threats.
Current adaptation gap: System adaptation (\(\tau \)_adapt ~ days-weeks) struggles against viral spread (\(\tau \)_threat ~ hours). Response: predictive nulling of categories rather than individual items.
Emerging failure modes: (1) Whack-a-mole problem — too many sources; (2) Streisand effect — suppression draws attention; (3) Platform alternatives — Telegram, Rumble reduce null effectiveness; (4) Credibility loss — fact-checker trust declining.
12.4.9 Synthesis: Current Locking State Assessment
Population Segments The following estimates are the author’s assessment informed by media trust survey trends (Gallup media confidence, Edelman Trust Barometer) mapped to locking-state categories. They are not direct measurements of “locking state” and should be treated as order-of-magnitude indicators.
|
Segment | Estimated % | Locking State | Primary Lock |
|
Firmly locked to mainstream | 30-40% | Stable lock | V_inj dominates |
|
Questioning but locked | 25-35% | Unstable lock | Near transition |
|
Actively unlocked | 15-25% | Independent oscillation | Counter-narrative |
|
Never locked | 5-10% | Always independent | High Q outliers |
- Historical: Near-universal lock (pre-internet)
- Current: Fragmenting, contested
-
Trend: Lock weakening due to:
- Declining V_inj effectiveness (trust collapse)
- Rising V_counter (alternative media)
- Increasing K (network connectivity)
- Rising average Q (meditation, awareness trends)
- Current estimate: 20-30% unlocked
- Cascade threshold: ~35-40%
- Timeline: Years, not decades (at current trajectory)
_________________________________
12.4.10 Source Mapping and Uncertainty Bands for Key Numeric Claims
The chapter’s aggregate percentages and thresholds are modeled assessments, not direct locking-state measurements. Treat them as scenario bands with explicit uncertainty:
|
Quantity | Central Estimate | Uncertainty Band | Basis |
|
Firmly locked segment | 35% | 30-40% | Media trust and narrative-alignment survey trends |
|
Questioning but still locked | 30% | 25-35% | Mixed-attitude cluster in longitudinal polling |
|
Actively unlocked | 20% | 15-25% | Alternative media adoption and self-report autonomy indicators |
|
Never locked outliers | 7% | 5-10% | Persistent low-conformity subgroup estimates |
|
Cascade onset threshold | 37.5% | 35-40% | Coupled-oscillator transition heuristic |
Confidence labeling:
- High: directly measured variable with repeated instrumentation.
- Medium: directly measured proxy mapped to model state.
- Low: inferred state without direct lock-state instrumentation.
Current chapter labels for these values: Low-Medium confidence. Use for planning ranges, not point forecasts.
_________________________________
12.5 Connections and Reading Path
Previous: Chapter 11 (Phased Array Humanity) — collective coherence dynamics and the \(N^2\) scaling advantage that injection locking exploits and disrupts
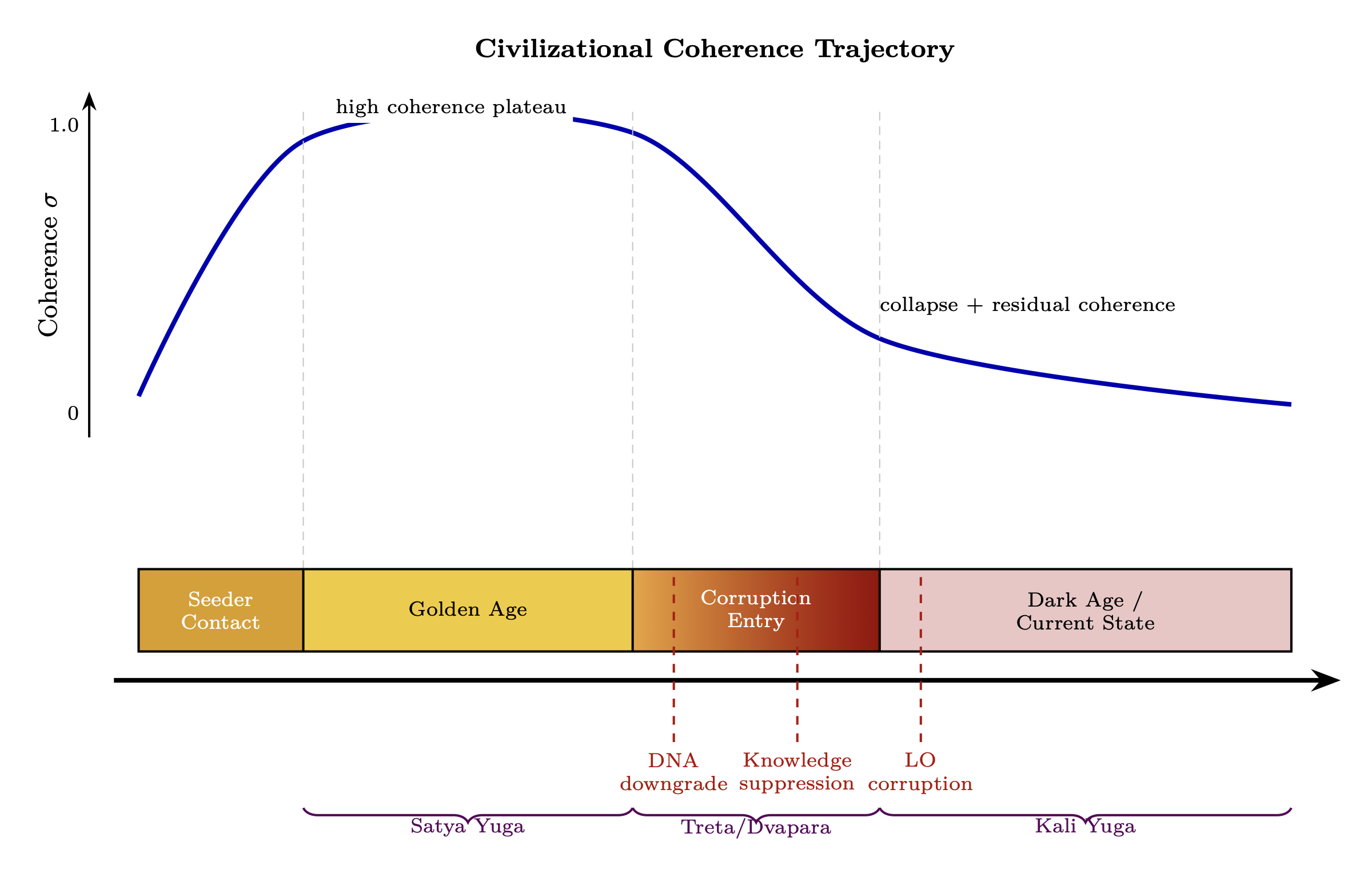
Next: Chapter 13 (Spin Coherence Fundamentals) — the master coherence variable \(\sigma \) that determines both array gain and lock vulnerability at the physical level
Key dependencies:
- Chapter 7 (Consciousness as RLC Circuit): Q = \(Z_0\)/R derivation; Q as primary sovereignty measure; \(Z_0\) as depth of processing
- Chapter 2 (Densities): Higher \(Z_0\) (higher frequency coupling) enables higher density access; Q determines lock resistance
- Chapter 11 (Phased Array Humanity): Coherence effects that amplify counter-injection; element quality and collective beam strength
- Chapter 16 (Paradigm Shielding): How injection power is maintained at the system level
- Chapter 17 (Counter-Jamming): Injection locking as component of total gain/loss in the link budget
_________________________________
End of Chapter 12: Injection Locking and Perception Management